10.6
In this topic, we reviewed the general delay-management architecture for the VoIP system and illustrated our work on delay analysis for utilization-based admission control that can effectively provide delay guarantee for VoIP traffic. We also presented our work on design and implementation of a delay-provisioning system that can be seamlessly integrated into the current Cisco VoIP system.
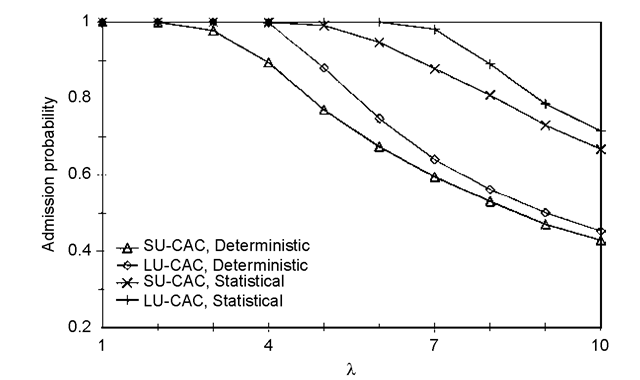
FIGURE 10.10 The admission probability in the campus network.
The integration of our proposed delay-provisioning system with existing VoIP systems has practical applicability for different types of networks: (1) Closed networks where all traffic is under control. Our system can directly work in such networks. (2) Semi-open networks, such as Internet2, where all highest priority traffic can be known, although it cannot be controlled. In our delay-provisioning system, voice traffic has the highest priority and low priority traffic has no impact on voice. Although VoIP is assigned the highest priority (the single real-time priority) in this topic, the theoretical results in our previous work [3-6] support systems with other applications which have a higher priority than VoIP applications. Our approach can still work by considering other higher priority traffic in the utilization computation. (3) Open networks, such as the Internet, where traffic cannot be controlled and is difficult to predict. Our approach can provide statistical guarantees as long as the traffic on the Internet can be modeled. To our knowledge, modeling Internet traffic is an open issue and is beyond the scope of this study. At the current stage, we can measure the Internet delay at the egress and ingress points of custom networks and dynamically change the bandwidth allocation at custom networks to compensate for the fluctuation of the delay in the Internet. Certainly, such an approach cannot provide guaranteed services. However, if the Internet delay (backbone delay) is small (a general case), the end-to-end delay is predictable.
non-worst case. Therefore, given the aggregated arrival traffic constraint function Fk(I) of all voice flows, we can specify the mean rate and the rate-variance envelope as a function of nk etc. Fk(I) is given as follows:
![tmp97-1_thumb[1] tmp97-1_thumb[1]](http://lh4.ggpht.com/_X6JnoL0U4BY/S4T5bH2HzdI/AAAAAAAAUWE/qTLZ2sdUC_I/tmp971_thumb1_thumb.png?imgmax=800)
At this point, the only undetermined variable is the number of flows on each link. In the following, we describe how we eliminate the dependency on the number of flows on each link. The result is a delay formula that can be applied without knowledge of the flow distribution.
As we described earlier, admission control at run time makes sure that the link utilization allocated to each class of flows is not exceeded. The total number nk of voice flows from all input links is therefore subject to the following constraint:
![tmp97-2_thumb[1] tmp97-2_thumb[1]](http://lh6.ggpht.com/_X6JnoL0U4BY/S4T5c6i-FTI/AAAAAAAAUWM/fCeL9A724_8/tmp972_thumb1_thumb.png?imgmax=800)
With this constraint, by (B-4) and (B-5), the mean rate and the rate variance can be upper bounded. Therefore, the deadline violation probability can be upper bounded without relying on the run-time information of flow distribution.
Conclusion (VoIP)
Next post: Introduction (VoIP)
Previous post: Performance Evaluation (VoIP)
