Understanding TCP/IP: More than just protocols
Many pieces of the TCP/IP suite have multiple functions: protocols, applications, and services. As we talk about all the useful things you can do with TCP/IP, we let you know whether you’re using a TCP/IP protocol, a service, or an application — and highlight the places where the same name applies to one or more of these concepts.
The layered design of TCP/IP works the same way as a new cake recipe does. Suppose that you’re a pastry chef and you create a new recipe for the cake components — the layers, the frosting, and the decorations. If you decide that you want to change the frosting to chocolate, you can simply swap out the vanilla recipe — no problem. You don’t have to change the layers or the decorations. At the same time, you’re thinking about using a new serving plate to show off your fabulous cake. When your cake is done baking, you serve your clients (friends and customers, for example), and they happily consume the result of your tasty baking service.
The layered design of TCP resembles baking a cake: You can easily add new components. If you’re a programmer who dreams up a new network service (such as applying the frosting) and then you design the client and server applications, you can simultaneously design a new protocol to add to the TCP/IP suite. The protocol enables the server application to offer the service and lets the client application consume that service. This level of simplicity is a key advantage of TCP/IP.
Determining whether your network has a protocol, an application, or a service
In a network, you find the protocol/application/service relationship so tightly bound together that you might have difficulty determining what’s what. We use the File Transfer Protocol, or FTP, as an example. It’s not only a protocol — it’s also a service and an application. (Don’t worry about FTP itself at this point — it’s just an example.In the following list, we show you how the FTP service, application, and protocol work together to move files on the network:
✓ FTP is a service for copying files: You connect to a remote computer running the FTP service, and you can then pull files from, or push files to, that computer.
Pull is a more technical term for download, and you may have already realized that push is a technical synonym for upload.
✓ FTP is also an application for copying files: You run a client application on your local computer to contact the FTP server service on the remote computer. The client application is either FTP or your Web browser. The browser uses the FTP protocol behind the scenes for downloads. The server application is known as the file transfer protocol daemon, or FTPD. (The term daemon comes from Unix — think of friendly demons haunting the computer to act on your behalf.) You tell the client what you want to do — pull or push files — and it works with the service to copy the files.
✓ Finally, FTP is a protocol for copying files: The client and server applications both use this to communicate, to ensure that the new copy of the file is, bit for bit and byte for byte, identical to the original.
FTP is an application, a service, and a protocol. Suppose that you need to copy a file from a remote computer. Without the application, your computer doesn’t know that you want to copy. Without the service, your computer doesn’t make a connection to the remote computer that has the files you need. Without the protocol, the client and server can’t communicate.
Most of the time, you know from the context whether someone is referring to the service, the application, or the protocol. If you can’t quite tell, maybe it doesn’t matter.
Plowing through the Protocol List (In Case You Thought Only Two Existed)
Hold on tight — here come the pieces in the TCP/IP protocol suite, listed by layer. We start at the bottom with Layer 1, the physical layer, and move to the top application layer, which has the highest number of protocols.
Physical layer protocols
The protocols in this hardware layer aren’t strictly TCP/IP protocols. Instead, they define how the hardware should be used to run a network. For example, the IEEE standards for Ethernet LAN (Local-Area Network) speeds and cables are in the physical layer. Don’t worry about this concept too much. Save your brainpower for reading about the upper-layer protocols.
Data link layer protocols
The data link layer moves data through the higher layers for transportation across networks and through tunnels to VPNs. The data link layer also includes MAC protocols that understand your network interface card.
Internet layer protocols
The internet layer is the third layer in our imaginary layer cake. IP is the most important protocol in not only the network layer but also the TCP/IP stack. Without IP, TCP wouldn’t know where to send anything.
IP: Internet Protocol
The Internet Protocol, IP, is responsible for basic network connectivity. IP resembles a plate in a basic place setting: When you’re eating, you need a plate to hold your food. When you’re networking, you need a place to put (send and receive) data — and that place is a network address.
The core of IP works with Internet addresses.Every computer on a TCP/IP network must have a numeric address. The IP protocol understands how and where to send messages to these addresses. In fact, all the other protocols — except for ARP and RARP — depend on IP to move information from one computer to another.
Although IP can take care of addressing, it can’t do everything to ensure that your information reaches its destination correctly and in one piece. IP doesn’t know (or care) when a packet of data gets lost and doesn’t arrive, so you need some other protocols to ensure that no packets and data are lost and that the packets are in the right order.
Two versions of IP exist: IP version 4 (IPv4) and IP version 6 (IPv6). When very large networks, such as the Internet, found IPv4 too restrictive, especially in terms of addressing and security, IPv6 (described next) was developed. Both versions of IP are in use across the Internet. Some sites use both. A common practice is to say "IP" to mean either IPv4 or IPv6, or both.
IPv6: Internet Protocol version 6
IPv6 is a bigger and better version of IPv4 that adds features. The IPv4 information (with certain modifications) also holds true for IPv6. (If IP is an Internet plate, IPv6 is an Internet serving platter.)
ARP: Address Resolution Protocol
ARP is the salad plate of the network place setting. With its load of addresses for the devices on the network, ARP works closely with IP, the dinner plate. When all you know about the remote computer is its TCP/IP address, the Address Resolution Protocol (ARP) finds the computer’s NIC hardware address. Every NIC comes with a unique MAC address built into it. You cannot change it. ARP is the coordinator between a NIC’s hard-coded MAC address and an IP address. By the way, ARP is a protocol, a service, and an application, although you rarely see the application.
RARP: Reverse Address Resolution Protocol
When a computer knows only its own MAC address, the Reverse Address Resolution Protocol (RARP) lets it find out the IP address it has been assigned. In addition to being a protocol, RARP is also a service. These days, the use of the Dynamic Host Configuration Protocol (DHCP) has mostly replaced RARP. In our dinner analogy, RARP is the salad fork that goes with the ARP salad plate. Okay, we realize we’re stretching the analogy a bit.
ICMP: Internet Control Message Protocol
ICMP reports problems and relays other network-specific information, such as an error status, from network devices. IP detects the error and sends it to ICMP. (It reminds us of a crystal goblet in our imaginary TCP/IP dinner-ware set.) The goblet "pings" when you hit it. In addition to being a protocol, ICMP is a service and an application, although the application is named ping.
Mobile IP
The proposed Mobile IP standard describes how you can connect your mobile device to the Internet from various locations, such as your office, hotel room, and car, while keeping the same IP address.
IPSec: IP Security Protocols
The IPSec protocols provide security services for other TCP/IP protocols and applications. For example, as the security protocol for VPNs, IPSec includes some strong encryption (coding) techniques to protect your data in the public and private world of VPNs. IPSec also ensures that the computer accessing your private network across the public Internet is truly a part of your network and not a pretender trying to sneak into your VPN.
L2TP: Layer 2 Tunneling Protocol
L2TP uses IPSec to encrypt messages moving through VPN tunnels.L2TP often replaces Point-to-Point Tunneling Protocol (PPTP), an older encryption protocol.
CIDR: Classless Inter-Domain Routing
CIDR is the beverage at the network table that helps addressing flow smoothly. Before IPv6 was developed, people worried that the Internet would run out of addresses. CIDR allows the more efficient allocation of IP addresses for the Internet and also helps in routing packets.
Transport layer protocols
The protocols in the transport layer include TCP and UDP and some of the routing protocols.
TCP: Transmission Control Protocol
If IP is the network "plate," TCP is the network "spoon." After food is plopped on your plate, you need something to send it into your mouth without spilling it into your lap. Sure, you could use a fork, but try eating soup with a fork. You can probably eat peas from your knife without dropping any, but a spoon is the most reliable implement for most Western foods.
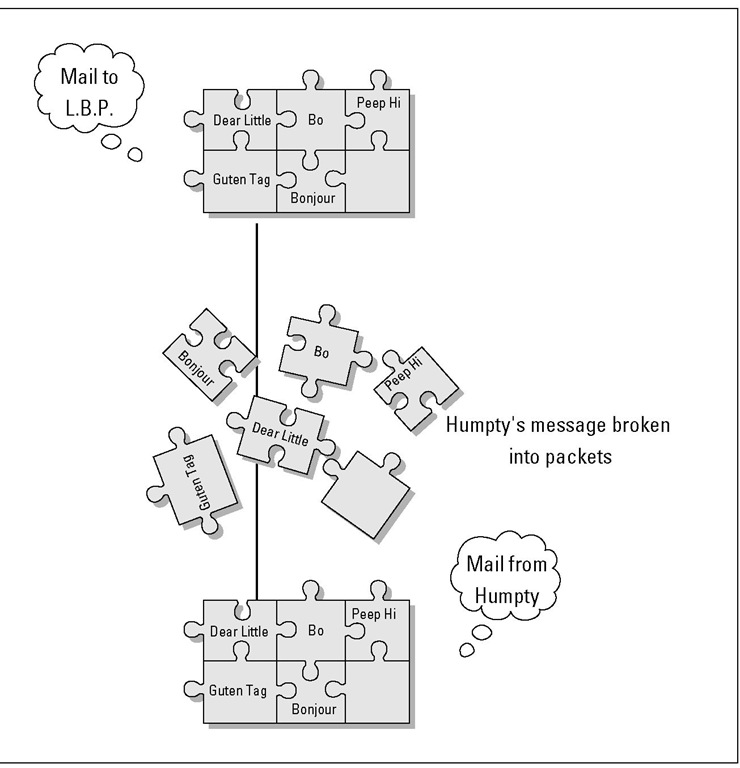
When your packets travel across a network, IP doesn’t promise that the packets will arrive in order. In fact, IP doesn’t even guarantee that all your packets will arrive. One or more packets may get dropped while on their trip from the source to the destination. IP doesn’t care — TCP takes care of it. Figure 2-6 shows how an e-mail message is "packetized," or sent across the Internet and reassembled.
Just like a spoon, TCP ensures that nothing is dropped, no matter what kind of data you’re sending. TCP uses IP to deliver packets reliably to those upper-layer applications. Two of the most important TCP functions are
✓ Error checking: Ensures that every packet arrives undamaged
✓ Sequence numbering: Puts the packets back into the right order. Refer to Figure 2-6 to see packet sequencing.
Figure 2-6:
TCP sequences packets correctly.
After a packet arrives at the correct IP address, TCP goes to work. It establishes a dialogue between the sending and receiving computers to communicate about the data that’s being transmitted. TCP is said to be connection oriented because it tells the network to resend lost data.
Theoretically, you can have TCP without IP. A network mechanism other than IP can deliver the data to an address, and TCP can still verify and sequence that data. But in practice, TCP is always used with IP.
UDP: User Datagram Protocol
UDP provides functions similar to TCP. The big difference is reliability. As mentioned, TCP does the best job of moving packets across a network. In our dinnerware analogy, where IP is the network plate and TCP is the network spoon, UDP is your Internet fork: Using it gets most of your food to your mouth, even if you drop some bites. Although it’s not as reliable as
TCP, UDP nevertheless moves a lot of data safely across the network. UDP uses IP to deliver packets to upper-layer applications and provides a flow of data among computers. The reason that UDP is less reliable than TCP as a transport protocol is that UDP provides neither error checking nor sequence numbering.
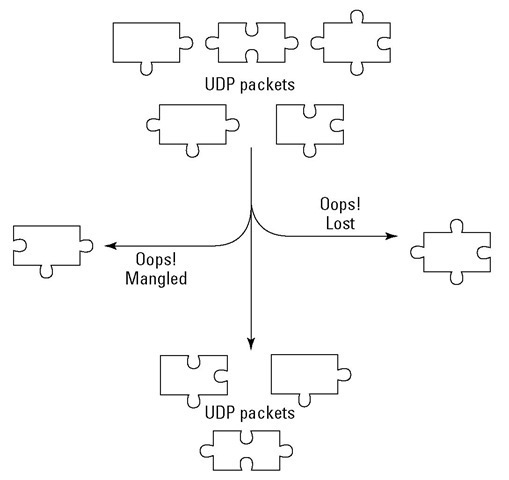
UDP is said to be connectionless because it doesn’t provide for resending data in case of error. Figure 2-7 illustrates one difference between UDP and TCP.
Figure 2-7: UDP might drop packets.
Another difference between TCP and UDP is that many TCP implementations are polite: They don’t intrude on a congested network — they wait before sending their packets. UDP, on the other hand, has no worries about network congestion. It rudely sends packets across even the most congested network. Some of the services and applications that use UDP include:
✓ Domain Name System (DNS)
✓ Network File System (NFS)
✓ SNMP (Simple Network Management Protocol)
✓ Various online games
✓ Voice over IP (VoIP)
Some protocols use both TCP and UDP. DNS runs on top of either TCP or UDP depending on packet delivery needs. For short messages, DNS uses UDP. For longer requests that require absolutely reliable delivery, DNS uses TCP.
TCP versus UDP: Connection oriented versus connectionless?
TCP/IP communicates among the layers in two different ways:
✓ Connection-oriented communication is reliable and easy to understand. When two computers are communicating with each other, they connect: Each one understands what the other one is doing. The sending computer lets the receiving computer know that data is on the way. The receiver then ACKs (acknowledges) or NACKs (denies or negatively acknowledges) receipt of the data. A receiver NACKs if the error checking shows a problem. A sender that receives neither an ACK nor a NACK assumes that the data was lost and automatically resends the data.
This process of ACKing and NACKing is known as handshaking.
Suppose that you send a fax to your friend Ken in Tokyo. If you want to be sure that he receives the fax, you might call and say, "I’m faxing you the baseball results now. Call me when they come through." After Ken receives the fax and ensures that it’s readable, he calls you and says, "Thanks. I’m thrilled to hear that the Red Sox finally won the World Series." That’s how TCP behaves.
✓ Connectionless communication occurs when you send a fax without first notifying your friend and, for some reason, it never reaches its destination. Ken doesn’t know to expect anything, so he doesn’t know that anything is lost. When data are sent via the connectionless method, the computers involved know nothing about each other or the data. If you’re on the receiving end, no one tells you that you’re about to receive anything. If you’re sending data, no one bothers to mention whether they received the document or whether it was garbled. That’s how UDP behaves.
With this information in mind, you might wonder why any applications use connectionless mode. But there’s a time and place for everything. First, communication is faster without the ACKs and NACKs. Second, not every network message needs to be as accurate as your e-mail messages. Finally, because some applications do their own error checking and reliability processing, they don’t need the connection-oriented overhead of TCP.
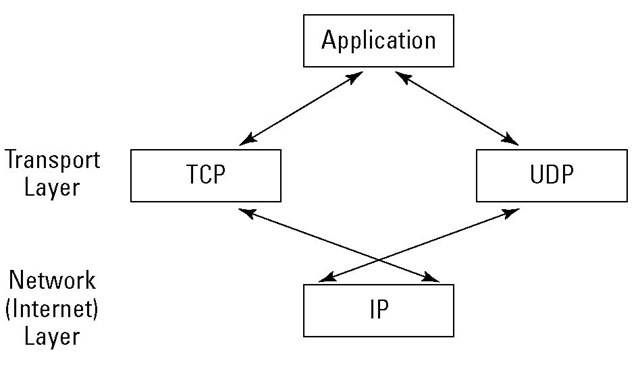
Figure 2-8 shows the packet beginning its trip at the physical layer. When the packet reaches the internet layer, one of two things happens:
✓ The packet takes the TCP path.
✓ The packet takes the UDP path.
The double-headed arrow shows that packets move up and down the layers.
Figure 2-8:
TCP and UDP pass IP packets to and from the applications.