Cryptography Reference
In-Depth Information
fr
y
f
+
1
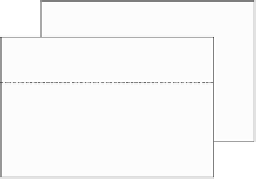
Frame
Region
Subregions:
(,,1)
fr
y
f
f
,1
f
,2
y
Frame
y
(,,)
frk
y
fr
y
fR
(,, )
frK
y
y
Region
Fig. 7.9.
An example of video partitioning.
′
(f,r,k)
Step E3: Generate each watermarked region y
by adding the WM pat-
. This is a pseudo
m
(k)
i
tern m
(k)
N
(RK)
=
∈−1, +11≤i≤
′
(f,r,k)
:
random array1s and introduced into the original region y
y
(f,r,k)
+ µ
(f,r)
m
(k)
, if b
k
=1,
y
(f,r,k)
−µ
(f,r)
m
(k)
, if b
k
=0,
′
(f,r,k)
y
=
(7.15)
where µ
(f,r)
is WM strength of the region y
(f,r)
.
Step E4: Output the watermarked frame y
′
(f )
.
WM detection
K correlation values c
k
s are calculated by correlating the WM pattern, m
(k)
,
with the accumulated subregion.
Step D1: Do the following steps over f
0
=1,F +1, 2F +1,.
Step D2: Input F watermarked frames y
′
(f )
s(f = f
0
,,f
0
+ F−1) and
then divide FRK subregions y
′
(f,r,k)
s(f = f
0
,,f
0
+ F−1,r =
1,,R,k =1,,K).
Step D3: For each k, where k =1,,K, accumulate the FR subregions
y
. The y
(k)
i
′
(f,r,k)
s in the subregion y
(k)
y
(k)
i
N
(RK)
=
1≤i≤
of the accumulated subregion y
(k)
is given by
f
0
+F−1
R
1
FR
y
(k)
i
′
(f,r,k)
i
=
y
.
(7.16)
f =f
0
r=1
Step D4: Calculate the set consisting of the K correlation values
c =c
k
1≤k≤K.
(7.17)
Each correlation value c
k
is obtained by correlating the WM pattern
m
(k)
with the accumulated subregion y
(k)
.Thatis,