Cryptography Reference
In-Depth Information
Calculate the accumulated metrics of the nodes at instant
i
:
μ
(
i,
0
)=min(
λ
(
T
(
i,
0
,
0
)
,λ
(
T
(
i,
1
,
0
))
μ
(
i,
1
)=min(
λ
(
T
(
i,
3
,
1
)
,λ
(
T
(
i,
2
,
1
))
μ
(
i,
2
)=min(
λ
(
T
(
i,
0
,
2
)
,λ
(
T
(
i,
1
,
2
))
μ
(
i,
3
)=min(
λ
(
T
(
i,
3
,
3
)
,λ
(
T
(
i,
2
,
3
))
For each of the four nodes of the trellis, the value of
d
i
corresponding to the
transition of minimum accumulated metric
λ
is stored in memory.
(0)
(1)
(2)
(
i
,
2
)
= min (
(
i
,
s
)
)
s
{0, 1, 2, 3}
(3)
i
15
i
14
i
13
i
2
i
1
i
d
i
15
Figure 5.21 - Survivor path traceback operation (in bold) in the trellis from instant
i
and determining the binary decision at instant
i −
15
.
After selecting the node with minimum accumulated metric, denoted
s
(in
the example of Figure 5.21,
s
=
3
), we trace back in the trellis along the survivor
path to a depth
l
=15
.Atinstant
i
15
, the binary decision
d
i−
15
is equal to
the value of
d
i−
15
stored in the memory associated with the survivor path.
The aim of applying the Viterbi algorithm with weighted inputs is to search
for codeword c that is the shortest Euclidean distance between two codewords.
Equivalently (see Chapter 1), this also means looking for the codeword that
−
m
.
i
=1
k
l
=1
l
=1
n
x
(
l
)
i
X
(
l
)
i
y
(
l
)
i
Y
(
l
)
i
maximizes the scalar product
x
,
X
+
y
,
Y
=
+
In this case, applying the Viterbi algorithm uses branch metrics of the form
d
(
T
(
i,
s
i−
1
,
s
i
)) =
l
=1
l
=1
m
n
x
(
l
)
i
X
(
l
)
i
y
(
l
)
i
Y
(
l
)
i
+
and the survivor path then corre-
sponds to the path with maximum accumulated metric.
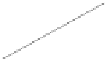
Figure 5.22 provides the performance of the two variants, with hard and
weighted inputs, of a decoder using the Viterbi algorithm for the code (7,5)
RSC for a transmission on a channel with additive white Gaussian noise. In
practice, we observe a gain of around 2 dB when we substitute weighted input
decoding for hard input decoding.