There are literally thousands of applications that run on the Internet and on other networks. Most application software that we develop today, whether for sale or for private internal use, runs on a network. We could spend years talking about different network applications and still cover only a small number.
Fortunately, most network application software works in much the same way as the Web or e-mail. In this section, we will briefly discuss only four commonly used applications: File Transfer Protocol (FTP), Telnet, instant messaging (IM), and Video conferencing.
File Transfer Protocol
File Transfer Protocol (FTP), is an old application that enables you to send and receive files over the Internet. FTP works in a similar manner as HTTP. FTP requires an application layer program on the client computer and a FTP server application program on a server. There are many software packages that use the FTP standard, such as WS-FTP. The user uses his or her client to send FTP requests to the FTP server. The FTP server processes these requests and sends back FTP packets containing the requested file.3
Most FTP sites require users to have permission before they can connect and gain access to the files. Access is granted by providing an account name with a password. For example, a network manager or Web-master would write a Web page using software on his or her client computer and then use FTP to send it to a specific account on the Web server.
A Day in the Life: Network Manager
It was a typical day for a network manager. It began with the setup and troubleshooting for a videoconference. Videoconferencing is fairly routine activity but this one was a little different; we were trying to video-conference with a different company who used different standards than we did. We attempted to use our usual web-based videoconferencing but could not connect. We fell back to ISDN-based videoconferencing over telephone lines, which required bringing in our videoconferencing services group. It took two hours but we finally had the technology working.
The next activity was building a Windows database server. This involved installing software, adding a server into our ADS domain, and setting up the user accounts. Once the server was on the network, it was critical to install all the security patches for both the operating system and database server. We receive so many security attacks that it is our policy to install all security patches on the same day that new software or servers are placed on the network or the patches are released.
After lunch, the next two hours was spent in a boring policy meeting. These meetings are a necessary evil to ensure that the network is well-managed. It is critical that users understand what the network can and can’t be used for, and our ability to respond to users’ demands. Managing users’ expectations about support and use rules helps ensure high user satisfaction.
The rest of the day was spent refining the tool we use to track network utilization. We have a simple intrusion detection system to detect hackers, but we wanted to provide more detailed information on network errors and network utilization to better assist us in network planning.
Telnet
Telnet enables users to log in to servers (or other clients). Telnet requires an application layer program on the client computer and an application layer program on the server or host computer. There are many programs that conform to the Telnet standard, such as EWAN. Once Telnet makes the connection from the client to the server, you must use the account name and password of an authorized user to login.
Because Telnet was designed in the very early days of the Internet, it assumes your client is a dumb terminal. Therefore, when you use Telnet, you are using a host-based architecture. All keystrokes you type in the Telnet client are transferred one by one to the server for processing. The server processes those commands—including simple keystrokes such as up arrow or down arrow—and transfers the results back to the client computer, which displays the letters and moves the cursor as directed by the server.4
Telnet can be useful because it enables you to access your server or host computer without sitting at its keyboard. Most network managers use Telnet to work on servers, rather than physically sitting in front of them and using their keyboards. Telnet also poses a great security threat, because it means that anyone on the Internet can attempt to log in to your account and use it as he or she wishes. Two commonly used security precautions are to prohibit remote logins via Telnet unless a user specifically asks for his or her account to be authorized for it and to permit remote logins only from a specific set of
Tagging People
MANAGEMENT FOCUS
Joseph Krull has a chip on his shoulder—well, in his shoulder to be specific. Krull is one of a small but growing number of people who have a Radio Frequency Identification (RFID) chip implanted in their bodies.
RFID technology has been used to identify pets, so that lost pets can be easily reunited with their owners. Now, the technology is being used for humans.
Krull has a blown left pupil from a skiing accident. If he were injured in an accident and unable to communicate, an emergency room doctor might misinterpret his blown pupil as a sign of a major head injury and begin drilling holes to relieve pressure. Now doctors can use the RFID chip to identify Krull and quickly locate his complete medical records on the Internet.
Critics say such RFID chips pose huge privacy risks because they enable any firms using RFID to track users such as Krull. Retailers, for example, can track when he enters and leaves their stores.
Krull doesn’t care. He believes the advantages of having his complete medical records available to any doctor greatly outweighs the privacy concerns.
Internet addresses. For example, the Web server for this topic will accept Telnet logins only from computers located in the same building.
Instant Messaging
One of the fastest growing Internet applications is instant messaging (IM). With IM, you can exchange real-time typed messages or chat with your friends. Some IM software also enables you to verbally talk with your friends in the same way as you might use the telephone or to use cameras to exchange real-time video in the same way you might use a videoconferencing system. Several types of IM currently exist, including ICQ and AOL Instant Messenger.
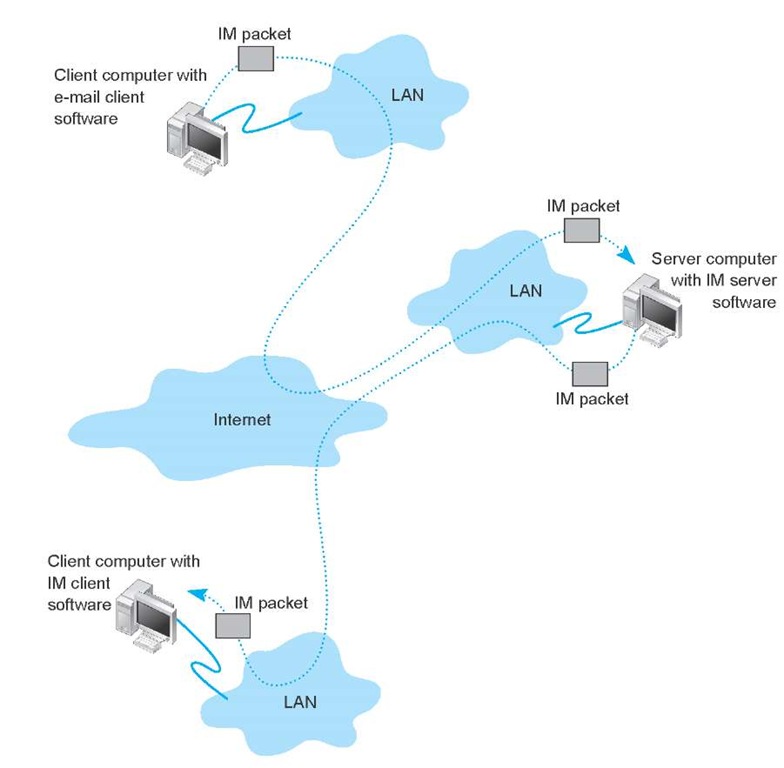
IM works in much the same way as the Web. The client computer needs an IM client software package, which communicates with an IM server software package that runs on a server. When the user connects to the Internet, the IM client software package sends an IM request packet to the IM server informing it that the user is now online. The IM client software package continues to communicate with the IM server to monitor what other users have connected to the IM server. When one of your friends connects to the IM server, the IM server sends an IM packet to your client computer so that you now know that your friend is connected to the Internet. The server also sends a packet to your friend’s client computer so that he or she knows that you are on the Internet.
With the click of a button, you can both begin chatting. When you type text, your IM client creates an IM packet that is sent to the IM server (Figure 2.15). The server then retransmits the packet to your friend. Several people may be part of the same chat session, in which case the server sends a copy of the packet to all of the client computers. IM also provides a way for different servers to communicate with one another, and for the client computers to communicate directly with each other. IM will also do Voice and Video.
Figure 2.15 How instant messaging (IM) works. LAN = local area network
Videoconferencing
Videoconferencing provides real-time transmission of video and audio signals to enable people in two or more locations to have a meeting. In some cases, videoconferences are held in special-purpose meeting rooms with one or more cameras and several video display monitors to capture and display the video signals (Figure 2.16). Special audio microphones and speakers are used to capture and play audio signals. The audio and video signals are combined into one signal that is transmitted though a MAN or WAN to people at the other location. Most of this type of videoconferencing involves two teams in two separate meeting rooms, but some systems can support conferences of up to eight separate meeting rooms. Some advanced systems provide telepresence, which is of such high quality that you feel you are face-to-face with the other participants.
The fastest growing form of videoconferencing is desktop videoconferencing. Small cameras installed on top of each computer permit meetings to take place from individual offices (Figure 2.17). Special application software (e.g., Yahoo IM, Net Meeting) is installed on the client computer and transmits the images across a network to application software on a videoconferencing server. The server then sends the signals to the other client computers that want to participate in the videoconference. In some cases, the clients can communicate with one another without using the server. The cost of desktop videoconferencing ranges from less than $20 per computer for inexpensive systems to more than $1,000 for high-quality systems.
figure 2.16 A Cisco tele presence system
Some systems have integrated conferencing software with desktop videoconferencing, enabling participants to communicate verbally and, by using applications such as white boards, to attend the same meeting while they are sitting at the computers in their offices.
The transmission of video requires a lot of network capacity. Most videoconferencing uses data compression to reduce the amount of data transmitted. Surprisingly, the most common complaint is not the quality of the video image but the quality of the voice transmissions. Special care needs to be taken in the design and placement of microphones and speakers to ensure quality sound and minimal feedback.
Most videoconferencing systems were originally developed by vendors using different formats, so many products were incompatible. The best solution was to ensure that all hardware and software used within an organization was supplied by the same vendor and to hope that any other organizations with whom you wanted to communicate used the same equipment. Today, three standards are in common use: H.320, H.323, and MPEG-2 (also called ISO 13818-2). Each of these standards was developed by different organizations and is supported by different products. They are not compatible, although some application software packages understand more than one standard. H.320 is designed for room-to-room videoconferencing over high-speed telephone lines. H.323 is a family of standards designed for desktop videoconferencing and just simple audio conferencing over the Internet. MPEG-2 is designed for faster connections, such as a LAN or specially designed, privately operated WAN.
Figure 2.17 Virtual Margaret
Webcasting is a special type of one-directional videoconferencing in which content is sent from the server to the user. The developer creates content that is downloaded as needed by the users and played by a plug-in to a Web browser. At present, there are no standards for Webcast technologies, but the products by RealNetworks.com are the de facto standards.