Routed Backbones
Routed backbones move packets along the backbone on the basis of their network layer address (i.e., layer-3 address). Routed backbones are sometimes called subnetted backbones or hierarchical backbones and are most commonly used to connect different buildings within the same campus network (i.e., at the core layer).
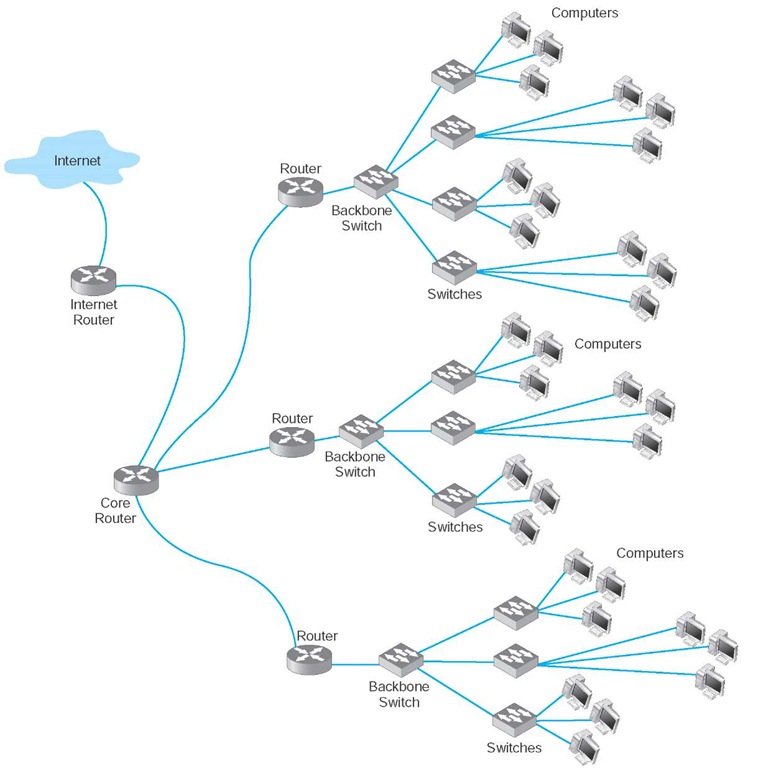
Figure 8.11 illustrates a routed backbone used at the core layer. A routed backbone is the basic backbone architecture we used to illustrate how TCP/IP worked in next topic. There are a series of LANs (access layer) connected to a switched backbone (distribution layer). Each backbone switch is connected to a router. Each router is connected to a core router (core layer). These routers break the network into separate subnets. The LANs in one building are a separate subnet. Message traffic stays within each subnet unless it specifically needs to leave the subnet to travel elsewhere on the network, in which case the network layer address (e.g., TCP/IP) is used to move the packet. For example, in a switched backbone, a broadcast message (such as an ARP) would be sent to every single computer in the network. A routed backbone ensures that broadcast messages stay in the one network segment (i.e., subnet) where they belong, and are not sent to all computers. This leads to a more efficient network.
Each set of LANs is usually a separate entity, relatively isolated from the rest of the network. There is no requirement that all LANs share the same technologies. Each set of LANs can contain its own server designed to support the users on that LAN, but users can still easily access servers on other LANs over the backbone as needed.
The primary advantage of the routed backbone is that it clearly segments each part of the network connected to the backbone. Each segment (usually a set of LANs or switched backbone) has its own subnet addresses that can be managed by a different network manager. Broadcast messages stay within each subnet and do not move to other parts of the network.
There are two primary disadvantages to routed backbones. First, the routers in the network impose time delays. Routing takes more time than switching, so routed networks can sometimes be slower. Second, routers are more expensive and require more management than switches.
Virtual LANs
For many years, the design of LANs remained relatively constant. However, in recent years, the introduction of high-speed switches has begun to change the way we think about LANs. Switches offer the opportunity to design radically new types of LANs. Most large organizations today have traditional LANs, but many are considering the virtual LAN (VLAN), a new type of LAN-BN architecture made possible by intelligent, high-speed switches.
Figure 8.11 Routed backbone design
VLANs are networks in which computers are assigned to LAN segments by software rather than by hardware. In the section above, we described how in rack-mounted collapsed BNs a computer could be moved from one hub to another by unplugging its cable and plugging it into a different hub. VLANs provide the same capability via software so that the network manager does not have to unplug and replug physical cables to move computers from one segment to another.
A Day in the Life: Network Operations Manager
The job of the network operations manager is to ensure that the network operates effectively. The operations manager typically has several network administrators and network managers that report to him or her and is responsible for both day-to-day operations as well as long-term planning for the network. The challenge is to balance daily firefighting with longer term planning; they’re always looking for a better way to do things. Network operations managers also meet with users to ensure their needs are met. While network technicians deal primarily with networking technology, a network operations manager deals extensively with both technology and the users.
A typical day starts with administrative work that includes checks on all servers and backup processes to ensure that they are working properly and that there are no security issues. Then it’s on to planning. One typical planning item includes planning for the acquisition of new desktop or laptop computers, including meeting with vendors to discuss pricing, testing new hardware and software, and validating new standard configurations for computers. Other planning is done around network upgrades, such as tracking historical data to monitor network usage, projecting future user needs, surveying user requirements, testing new hardware and software, and actually planning the implementation of new network resources.
One recent example of long-term planning was the migration from a Novell file server to Microsoft ADS file services. The first step was problem definition; what were the goals and the alternatives? The key driving force behind the decision to migrate was to make it simpler for the users (e.g., now the users do not need to have different accounts with different passwords) and to make it simpler for the network staff to provide technical support (e.g., now there is one less type of network software to support). The next step was to determine the migration strategy: a Big Bang (i.e., the entire network at once) or a phased implementation (several groups of users at a time). The migration required a technician to access each individual user’s computer, so it was impossible to do a Big Bang. The next step was to design a migration procedure and schedule whereby groups of users could be moved at a time (e.g., department by department). A detailed set of procedures and a checklist for network technicians were developed and extensively tested. Then each department was migrated on a one week schedule. One key issue was revising the procedures and checklist to account for unexpected occurrences during the migration to ensure that no data were lost. Another key issue was managing user relationships and dealing with user resistance.
VLANs are often faster and provide greater opportunities to manage the flow of traffic on the LAN and BN than do the traditional LAN and routed BN architecture. However, VLANs are significantly more complex, so they usually are used only for large networks.
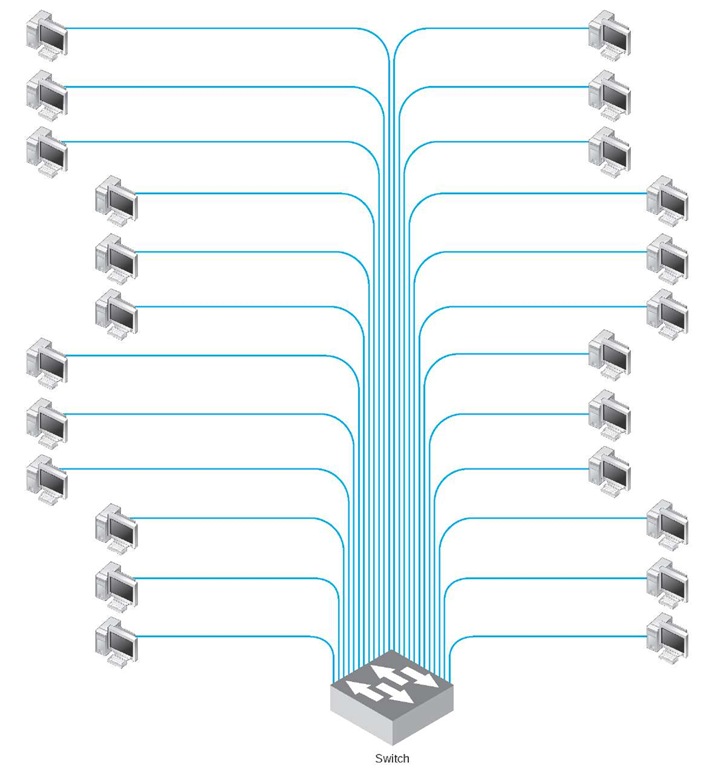
The simplest example is a single-switch VLAN, which means that the VLAN operates only inside one switch. The computers on the VLAN are connected into the one switch and assigned by software into different VLANs (Figure 8.12). The network manager uses special software to assign the dozens or even hundreds of computers attached to the switch to different VLAN segments. The VLAN segments function in the same way as physical LAN segments or subnets; the computers in the same VLAN act as though they are connected to the same physical switch or hub in a certain subnet. Because VLAN switches can create multiple subnets, they act like layer-3 switches or routers,except the subnets are inside the switch, not between switches. Therefore, broadcast messages sent by computers in one VLAN segment are sent only to the computers on the same VLAN.
Figure 8.12 VLAN-based backbone network design
VLANs can be designed so that they act as though computers are connected via hubs (i.e., several computers share a given capacity and must take turns using it) or via switches (i.e., all computers in the VLAN can transmit simultaneously). Although switched circuits are preferred to the shared circuits of hubs, VLAN switches with the capacity to provide a complete set of switched circuits for hundreds of computers are more expensive than those that permit shared circuits.
We should also note that it is possible to have just one computer in a given VLAN. In this case, that computer has a dedicated connection and does not need to share the network capacity with any other computer. This is commonly done for servers.
Benefits of VLANs Historically, we have assigned computers to subnets based on geographic location; all computers in one part of a building have placed in the same subnet. With VLANs, we can put computers in different geographic locations in the same subnet. For example, in Figure 8.12 a computer in the lower left could be put on the same subnet as one in the upper right—a separate subnet from all the other computers.
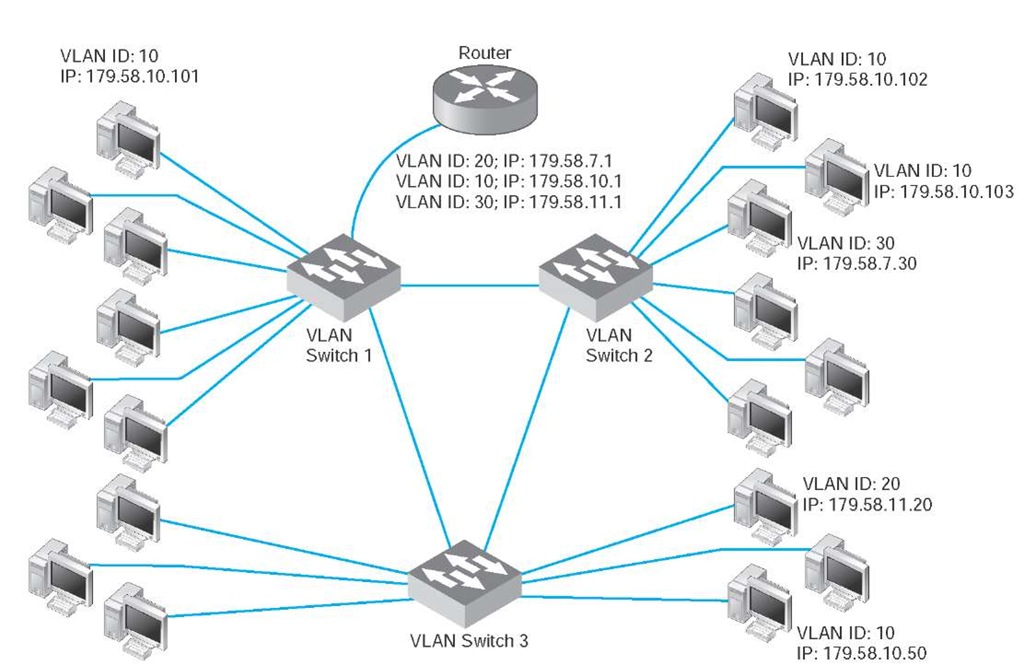
A more common implementation is a multi switch VLAN, in which several switches are used to build the VLANs (Figure 8.13). VLANs are most commonly found in building backbone networks (i.e., access and distribution layers) but are starting to move into core backbones between buildings. In this case, we can now create subnets that span buildings. For example, we could put one of the computers in the upper left of Figure 8.13 in the same subnet as the computers in the lower right, which could be in a completely different building. This enables as to create subnets based on who you are,rather than on where you are; we have an accounting subnet and a marketing subnet, not a building A and a building B subnet. We now manage security and network capacity by who you are, not by where your computer is. Because we have several subnets, we need to have a router—but more on that shortly.
Figure 8.13 Multi switch VLAN-based backbone network design
VLANs offer two other major advantages compared to the other network architectures. The first lies in their ability to manage the flow of traffic on the LAN and backbone very precisely. VLANs make it much simpler to manage the broadcast traffic that has the potential to reduce performance and to allocate resources to different types of traffic more precisely. The bottom line is that VLANs often provide faster performance than the other backbone architectures.
The second advantage is the ability to prioritize traffic. The VLAN tag information included in the Ethernet packet defines the VLAN to which the packet belongs and also specifies a priority code based on the IEEE 802.1q standard.As you will recall from next topic, the network and transport layers can use RSVP quality of service (QoS), which enables them to prioritize traffic using different classes of service. RSVP is most effective when combined with QoS capabilities at the data link layer. (Without QoS at the hardware layers, the devices that operate at the hardware layers [e.g., layer-2 switches] would ignore QoS information.) With the Ethernet packet’s ability to carry VLAN information that includes priorities, we now have QoS capabilities in the data link layer. This means we can connect VOIP telephones directly into a VLAN switch and configure the switch to reserve sufficient network capacity so that they will always be able to send and receive voice messages.
The biggest drawbacks to VLANs are their cost and management complexity. VLAN switches also are much newer technologies that have only recently been standardized. Such "leading-edge" technologies sometimes introduce other problems that disappear only after the specific products have matured.
Vlan Network at iona
MANAGEMENT FOCUS
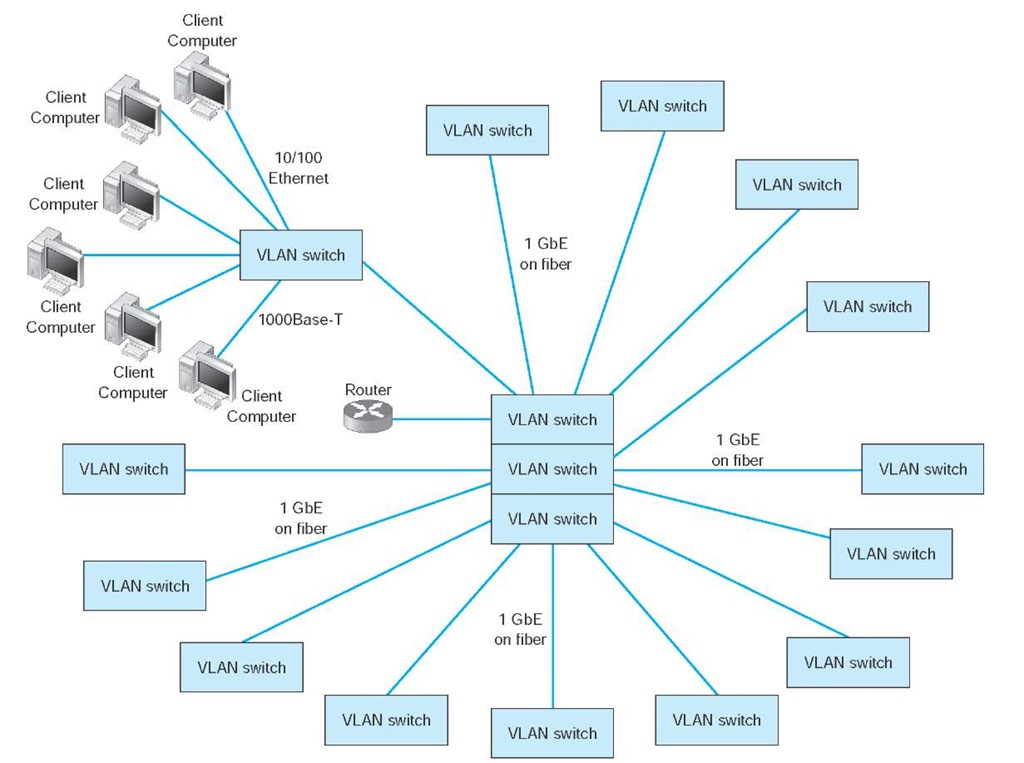
IONA Technologies, Inc., a 600-person software developer of enterprise middleware, took advantage of its relocation to Waltham, Massachusetts, to redesign its network infrastructure. The new network, designed to support 230 users in one office complex, uses a multiswitch virtual local area network (VLAN) architecture.
IONA has 27 access-layer VLAN switches located close to its users — built into their cubicle walls, to be exact. Up to 24 users are connected to each access-layer switch, using a mixture of 10/100 Ethernet and 1000Base-T over copper cables (e.g., category 5e) (Figure 8.14). Each of the first-level switches are connected via gigabit Ethernet over fiber to a central set of five VLAN switches that form the core of the network. IEEE 802.1q is used to communicate among the access-layer switches and the distribution-layer switches.
Because both the access-layer switches and distribution-layer switches are modular, it is easy for IONA to upgrade when technologies change.
Figure 8.14 IONAVLAN (virtual local area network)
How VLANs Work VLANs work somewhat differently than the traditional Ethernet/IP approach described in the previous topics. Each computer is assigned into a specific VLAN that has a VLAN ID number (which ranges from 1 to 1005 or to 4094 depending on whether the extended range standard is used). Each VLAN ID is matched to a traditional IP subnet, so each computer connected to a VLAN switch also receives a traditional IP address assigned by the VLAN switch. Most VLAN switches can support only 255 separate VLANs simultaneously, which means each switch can support up to 255 separate IP subnets, which is far larger than most organizations want in any single device.
Computers are assigned into the VLAN (and the matching IP subnet) based on the physical port on the switch into which they are connected.2 Don’t confuse the physical port on the switch (which is the jack the cable plugs into) with the TCP port number from next topic; they are different—it’s another example of networking using the same word ("port") to mean two different things. The network manager uses software to assign the computers to specific VLANs using their physical port numbers so it is simple to move a computer from one VLAN to another.
When a computer transmits an Ethernet frame, it uses the traditional Ethernet and IP addresses we discussed in previous topics to move the frame through the network because it doesn’t know that it is attached to a VLAN switch. Recall that as a message moves through the network, the IP address is used to specify the final destination and the Ethernet address is used to move the message from one computer to the next along the route to the final destination. Some devices, such as layer-2 switches, are transparent; the Ethernet frame passes through them unchanged. Other devices, such as routers, remove the Ethernet frame and create a new Ethernet frame to send the message to the next computer. VLANs are transparent—although they do change the frame at times.
Let’s use Figure 8.13 to explain how VLAN switches work. We’ll assume this network uses the first three bytes to specify the IP subnet. In this example, we have three VLAN switches with three IP subnets (179.58.10.x, 179.58.3.x, and 179.58.11.x) and three VLANs (10, 20, 30). A router is used to enable communication among the different IP subnets.
Suppose a computer connected to switch 2 (IP 179.58.10.102) sends a message to a computer on the same IP subnet that is also connected to switch 2 (IP 179.58.10.103). The sending computer will recognize that the destination computer is in the same IP subnet, create an Ethernet frame with the destination computer’s Ethernet address (using ARP if needed to find the Ethernet address), and transmit the frame to VLAN switch 2. When a VLAN switch receives a frame that is destined for another computer in the same subnet on the same VLAN switch, the switch acts as a traditional layer-2 switch: it forwards the frame unchanged to the correct computer. Remember from next topic that switches build a forwarding table that lists the Ethernet address of every computer connected to the switch. When a frame arrives at the switch, the switch looks up the Ethernet address in the forwarding table, and if it finds the address, then it forwards the frame to the correct computer. We discuss what happens if the Ethernet address is not in the forwarding table in a moment.
Suppose that a computer wants to send a message to a computer in the same subnet, but that the destination computer is actually on a different VLAN switch. For example in Figure 8.13, suppose this same computer (IP 179.58.10.102) sends a message to a computer on switch 3 (179.58.10.50). The sending computer will act exactly the same because to it, the situation is the same. It doesn’t know where the destination computers is; it just knows that the destination is on its own subnet. The sending computer will create an Ethernet frame with the destination computer’s Ethernet address (using ARP if needed to find the Ethernet address) and transmit the frame to VLAN switch 2. Switch 2 receives the frame, looks up the destination Ethernet address in its forwarding table, and recognizes that the frame needs to go to switch 3.
VLAN switches use Ethernet 802.1q tagging to move frames from one switch to another. Next topic showed that the layout of an Ethernet frame contains a VLAN tag field which VLAN switches use to move frames among switches. When a VLAN switch receives an Ethernet frame that needs to go to a computer on another VLAN switch, it changes the Ethernet frame by inserting the VLAN ID number and a priority code into the VLAN tag field. When a switch is configured, the network administrator defines which VLANs span which switches and also defines VLAN trunks—circuits that connect two VLAN switches and enables traffic to flow from one switch to another. As a switch builds its forwarding table, it receives information from other switches and inserts the Ethernet addresses of computers attached to them into its forwarding table along with the correct trunk to use to send frames to them.
In this case, switch 2 receives the frame, and uses the forwarding table to identify that it needs to send the frame over the trunk to switch 3. It changes the frame by inserting the VLAN ID and priority code into the tag field and transmits the frame over the trunk to switch 3. Switch 3 receives the frame, looks the Ethernet address up in its forwarding table, and identifies the specific computer the frame needs to be sent to. The switch removes the VLAN tag information and transmits the revised frame to the destination computer. In this way, neither the sending computer nor the destination computer are aware that the VLAN exists. The VLAN is transparent.
Suppose the same sending computer (179.58.10.102) wants to send a message to a computer on a different subnet in the same VLAN (e.g., 179.58.7.30 on the same switch or 179.58.11.20 on switch 3). The sending computer recognizes that the destination is on a different subnet, and therefore creates an Ethernet frame with a destination Ethernet address of its router (179.58.10.1), and sends the frame to switch 2.
At this point, everything works the same as in the previous example. Switch 2 looks up the destination Ethernet address in its forwarding table, and recognizes that the frame needs to go to switch 1 because the router’s Ethernet address is listed in the forwarding table as being reachable through switch 1. Switch 2 sets the VLAN tag information and sends the frame over the trunk to switch 1. Switch 1 looks up the destination Ethernet address in its forwarding table, and sees that the router is attached to it. Switch 2 removes the VLAN tag field and sends the frame to the router.
The router is a layer-3 device, so when it receives the message, it strips off the Ethernet frame and reads the IP packet. It looks in its routing table and sees that the destination IP address is within a subnet it controls (either 179.58.7.x or 179.58.11.x depending on which destination computer the packet was sent to). The router creates a new Ethernet frame and sets the destination Ethernet address to the destination computer (using an ARP if needed) and sends the frame to switch 1.
Switch 1 reads the Ethernet address and looks it up in its forwarding table. It discovers the frame needs to go to switch 2 (for 179.58.7.30) or switch 3 (for 179.58.11.20), sets the VLAN tag field, and forwards the frame over the trunk to the correct switch. This switch in turn removes the VLAN tag information and sends the frame to the correct computer.
Up to this point, we’ve been talking about unicast messages—messages from one computer to another—that are the majority of network traffic. However, what about broadcast messages such as ARPs that are sent to all computers in the same subnet? Each computer on a VLAN switch is assigned into a subnet with a matching VLAN ID. When a computer issues a broadcast message, the switch identifies the VLAN ID of the sending computer and then sends the frame to all other computers that have the same VLAN ID. These computers may be on the same switch, or on different switches. For example,suppose computer 179.58.10.102 issues an ARP to find an Ethernet address (e.g., the router’s address). Switch 2 would send the broadcast frame to all attached computers with the same VLAN ID (e.g., 179.58.10.103). Switch 2′s trunking information also tells it than VLAN 10 spans switch 1 and switch 3, so it sends the frame to them. They, in turn, use their tables to send it to their attached computers that are in the same VLAN (which includes the router). Note that the router has multiple IP addresses and VLAN IDs because it is connected to several different VLANs and subnets (three, in our example here).
We have also assumed that the VLAN switch has a complete forwarding table—a table that lists all the Ethernet addresses of all the computers in the network. Just like a layer-2 switch, the VLAN switch learns Ethernet addresses as it sends and receives messages. Where the VLAN switch is first turned on, the forwarding table is empty, just like the forwarding table of a layer-2 switch; however, its VLAN ID and trunk tables are complete because these are defined by the network administrator. Suppose the switch has just been turned on and has an empty forwarding table. It receives an Ethernet frame, looks up the destination address in the forwarding table, and does not find where to send it. What happens?
If the VLAN switch were a layer-2 switch, it would send the frame to all ports. However, a VLAN switch can be a bit smarter than this. If you think about how IP works, you will see that an Ethernet frame is always sent to a computer in the same IP subnet as the sending computer. Any time a frame needs to move to a different subnet, it goes through a router which sits on both subnets. Think about it for a minute before you continue reading. Therefore, any time the VLAN switch can’t find a destination Ethernet address in the forwarding table, it treats the frame as a broadcast frame and sends it to all the computers in the same subnet, which in VLAN terms means all the computers with the same VLAN ID.
This means that a VLAN architecture can improve performance by reducing traffic in the network compared with a switched backbone architecture. Since a switched backbone uses layer-2 switches, all the computers are in the same subnet, and all broadcast traffic goes to all computers. By using a VLAN we can limit where broadcast traffic flows by dividing the network into separate subnets, so that broadcast messages only go to computers in the same subnet.