Cryptography Reference
In-Depth Information
if a cryptosystem,
T
(and per-
haps an inverse system,
T'
),
could be devised that used
two keys and satisfied the fol-
lowing conditions:
• It must be easy for the
cryptographer to cal-
culate a matched pair
of keys,
e
(encryption)
and
d
(decryption),
for which
T
e
T'
d
=
I
.
Although not essen-
tial, it is desirable that
T'
d
T
e
=
I
and that
T
=
T'
.
Since most of the sys-
tems devised to meet
points 1-4 satisfy these
conditions as well, we
will assume they hold
hereafter—but that is
not necessary.
• The encryption and
decryption operation,
T
, should be (computa-
tionally) easy to carry out.
• At least one of the keys must be computation-
ally infeasible for the cryptanalyst to recover
even when he knows
T
, the other key, and arbi-
trarily many matching plaintext and ciphertext
pairs.
• It should not be computationally feasible to
recover
x
given
y
, where
y
=
T
k
(
x
) for almost all
keys
k
and messages
x
.
Given such a system, Diffie and Hellman proposed
that each user keep his decryption key secret and publish
his encryption key in a public directory. Secrecy was not
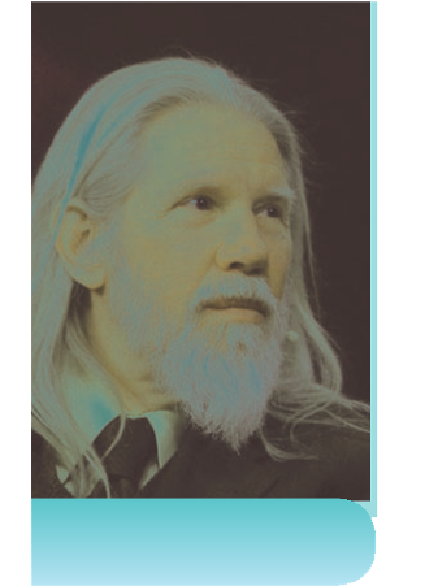
Whitfield Diffie.
Gabriel
Bouys/AFP/Getty Images