Cryptography Reference
In-Depth Information
the bytes which they take as input (and those they produce as output) have differ-
ent formats. In order to make these functions composable, we use the functions
bitstobyte
and
bytetobits
which are defined in Appendix A.
ByteSub
takes as input one byte given as an integer in the 0
..
255 range and produces as output
another byte given in the same format:
> ByteSub := bitstobyte@affmap@bytetobits@invbyte:
For example, let us compute the result of applying
ByteSub
to a few bytes (in
Maple versions prior to v13, the elementwise operator ~ should be replaced by a call
to
map
):
> ByteSub
∼
([$127 .. 132]);
[210, 205, 12, 19, 236, 95]
Now, the S-box can be given as a byte array such that, if
b
is a byte in the 0
..
255
range, then
ByteSub(b) = SBox[b]
:
> SBox := Array(0 .. 255, x-> ByteSub(x)):
We also record the following version of
SBox
, given as a map, which is useful,
for example, when one has to apply the
SBox
to the members of a list:
> SB := byte -> SBox[byte]:
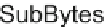
Remark 4.1
Observe that
ByteSub
and
SBox
are simply two different ways of
describing the permutation underlying the
SubBytes
transformation of AES. In
our subsequent implementation we will use
SBox
as a lookup table, which produces
much faster results than applying
ByteSub
. Note also that
SubBytes
is simply
the result of replacing each byte
b
in the state by
SBox[b]
(or, equivalently, by
ByteSub(b)
or
SB(b)
). We do not use the
SubBytes
name for this permutation
of the byte space, but rather for the operation that defines when it acts on the whole
state as illustrated by the following figure:
16 matrix with files and
columns numbered from 0 to 15. It is also customary to use hexadecimal notation for
this table so that files and columns are numbered by hexadecimal digits, from
0
to
f
.
Thus this matrix has files and columns numbered by “half-bytes” and its entries are
bytes. In this table, the image of the byte
b=ij
, where
i
and
j
are two hexadecimal
The S-box is usually displayed as a table given by a 16
×