Cryptography Reference
In-Depth Information
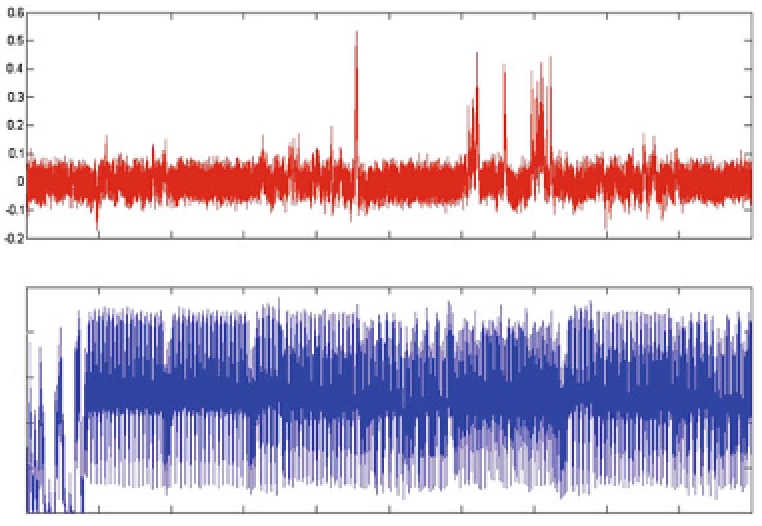
Fig. 1.7
An example of Differential Power Analysis applied to AES. The lower trace is an example
power consumption trace, and the upper trace is the correlation between the Hamming weight of
the output of one byte of the SubBytes function and a series of power consumption traces
countermeasures against physical attacks. The precise description of these counter-
measures and the advanced attacks that can be applied to circumvent them is out of the
scope of this chapter. But for completeness, we list certain types of countermeasures,
with pointers to further readings.
Regular Algorithms.
The information available to an attacker analyzing one trace
needs to be limited to the identification of operations, without revealing any informa-
tion on cryptographic keys. The simplest countermeasure is to use regular algorithms
that will compute the same sequence of operations for all possible key values. When
computing an RSA signature an alternative is to ensure that the same function is used
to compute both operations [85]. This was proposed to allow the continued use of
Algorithm 1.1, which is preferable on devices with limited resources. The rest of the
countermeasures described in this section apply to DPA.
Data Randomization.
The most investigated countermeasure to side-channel
analysis is masking (see, e.g. [168, 347]). The intuitive idea behind masking is
to split the sensitive data into a number of shares and to perform the encryption
operation on the different shares separately. As a consequence, any successful DPA
will have to combine the information from several shares (and, if not computed
in parallel, time samples) in order to observe key dependencies in the leakages.
Attacks on implementations using masking are referred to as 'higher-order' attacks,
and Chari et al. showed in [81] that the number of traces required to recover a key
from the leakages of a masked implementation increases exponentially in the num-
ber of shares, given that a sufficient amount of noise is limiting the quality of the
measurements [385]. Masking does not directly impact fault attacks, besides the fact