Cryptography Reference
In-Depth Information
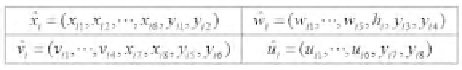
FIGURE 15.2
The format of stego-block
B
ij
with the size of 2 2 gray-level pixels.
FIGURE 15.3
Stego-block B
ij
used in Yang et al. which is revised from Figure 15.2, where
hash is used in the pixel of wˆi
i
= (w
i1
; ;w
i5
;h
i
;y
i3
;y
i4
).
v
i
= (v
i1
;v
i2
; ;v
i5
, y
i6
;y
i7
;y
i8
),
and u
i
= (u
i1
;u
i2
; ;u
i5
;y
i6
;y
i7
;y
i8
),
where b0
i
is the parity bit, which is chosen to make
w
i
including the cor-
B
ij
is shown in Figure
responding bit-string bi.
i
. The format of stego-block
15.2.
B
ij
generated in the Step 3 to create stego-image I
j
.
Step 4. Collect
15.3.3 Yang et al.'s Scheme
As observed from the Lin-Tsai scheme, the fake shares can be easily
made by the manner of fixing the parity bit b′i.
0
i
. For example, if a
i
=
(w
i1
;w
i2
; ;w
i5
;b
0
i
;y
i1
,y
i2
) = (0; 0; 1; 1; 1; 0; 1; 1), the parity bit b
0
i
is all the
same when the original wˆi
i
is changed to a new wˆi
i
as w
i
= (1; 0; 1; 1; 1; 0; 0; 1).
In such a way, the malicious attackers can easily modify w
i
0
s in the stego-
image to pass the authentication detection. As a result, the revelation of the
target secret image is not a right one. Next, Yang et al. [12] proposed a revised
version to set a new check function, e.g., hash function, instead of parity bit
in [4]. The stego-block B
ij
in [4] is then revised as the format shown in Figure
15.3. As analyzed in Yang et al., the probability of passing the detection with
the fake share offers is (
2
)
m
2
.
15.3.4 Inverted Pattern LSB Scheme
In order to conceal the existence of shadow data, steganographic methods
are used to keep the shadows imperceptible. The steganographic method is a
kind of data hiding technique that embeds secret data in preselected mean-
ingful images, called cover images, with people being visually unaware of the
secret's existence. One common technique to achieve the data hiding is the
LSB-based approach, in which secret data are embedded by directly replacing
the least significant bits (LSBs) with equal bits of the secret for each pixel.








Search WWH ::

Custom Search