Database Reference
In-Depth Information
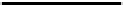
Fig. 3.
Original image (left side) and applied watermarking scheme of Merkel et al. (right side) [22]
Watermarking Scheme of Merkel et al.
As we implemented a variant of the water-
marking scheme of Merkel et al. [22] for our motivating example, we will introduce
the techniques of this scheme in more detail. Basically, this scheme uses compression
and difference expansion. In Figure 3, we depict an original (on the left side) and a
watermarked image of a finger print (right side) on a hard disk platter. Because this
scheme was developed to ensure the privacy of a fingerprint as well as the authenticity,
and integrity of the image and of the embedded data, it compresses and encrypts the
pixels in the area containing the fingerprint. Furthermore, this visible
2
compression is
used to embed parts of the watermark message. To ensure the integrity of the image and
the embedded data, the scheme uses signatures and hashes (H). Particularly, the signa-
ture S is computed as
S
=
E
(
H
(
Image
)
|Message
)
and embedded into the image as
well, where E is some cryptographic function. To restore the image, the retrieval phase
of the scheme has to know which parts of the image are compressed and encrypted.
This information (location map) is embedded into the image as well using the invisible
difference expansion technique of Coltuc [8].
Difference expansion.
Techniques, such as Tian's [28] and Coltuc's scheme [8] in-
crease the difference of the colour values of pixel pairs or blocks of pixels. Since we
implemented the scheme of Merkel et al. that uses Coltuc's fast embedding technique to
show the feasibility of our idea, we will briefly explain this technique. To apply Coltuc's
scheme, the algorithm initially splits the image into a set of pixel pairs
, accord-
ing to rows, columns or any space-filling curve. Second, the algorithm performs the
difference expansion of each pair using Equation 1 to compute the new pair
(
x, y
)
(
x
,y
)
.
t
(
x, y
)=(
x
,y
)
as x
=2
x −yy
=2
y − x
(1)
To embed a bit of the watermark message, Colutc's scheme modifies the transformation
t
of Equation 1 as shown in Equation 2. The bit of the watermark is embedded into the
least significant bit (LSB) of
y
. Furthermore, the scheme sets the LSB of
x
to one if
x
and
y
are even; else the LSB of
x
is set to zero. The marking of the LSB of the
x
values is important for the inverse transformation.
t
(
x, y, w
)=(
x
,y
)
,w∈{
0
,
1
} as x
=
u
(2
x − y, x, y
)
y
=2
y − x
+
w
x
temp
∨
1
,
if
x
and
y
even,
x
=
u
(
x
temp
,x,y
)=
x
temp
∧¬
1
else.
(2)
2
For invisible compression based schemes refer to Celik et al. [6]