Information Technology Reference
In-Depth Information
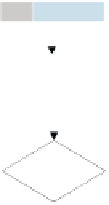
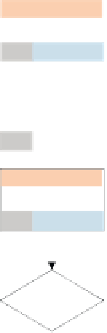
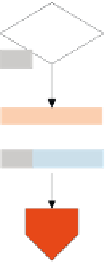
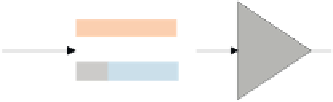
,QFLGHQW0DQDJHPHQW3UR]HVV
$EODXIGLDJUDPP
7LFNHWV\V
5FNPHOGXQJDQ
$QZHQGHU
0HOGXQJJHKWLP
/HYHOHLQ
7LFNHWDQOHJHQ
/HYHO
(0DLO
&DOO
)D[
6\VWHP
PHOGXQJ
7LFNHWV\V
.DWHJRULVLHUHQ
/HYHO
5HTXHVW
)XOILOOPHQW
-$
6HUYLFH
5HTXHVW"
1(,1
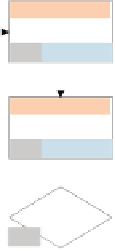
7LFNHWV\V
,QIR]X$XVZLUNXQJHQ
XQG3ULRULWLW
3ULRULVLHUHQ
/HYHO
7LFNHWV\V
-$
(LQIDFKO|V
EHNDQQW"
/|VXQJVYRUVFKODJ
DQ$QZHQGHU
/HYHO
1(,1
7LFNHWV\V
'XUFKIKUXQJ
/|VXQJVYRUVFKODJ
$QZHQGHU
7LFNHWV\V
.QRZQ(UURUV
:LVVHQVGDWHQEDQN
6W|UXQJVPXVWHU
XQWHUVXFKHQ
/HYHO
7LFNHWV\V
1(,1
/|VXQJVYHUVXFK
GRNXPHQWLHUHQ
/HYHO
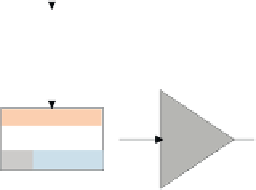
(UIROJUHLFK"
-$
7LFNHWV\V
0DMRU
,QFLGHQW
-$
/|VXQJ
GRNXPHQWLHUHQ
/HYHO
0DMRU
,QFLGHQW"
1(,1
7LFNHWV\V
-$
/|VXQJ
EHNDQQW"
/|VXQJ
EHUHLWVWHOOHQ
/HYHO
1(,1
7LFNHWV\V
:HLWHUOHLWXQJ
/HYHO
/HYHO
ABBILDuNG 8.10
EPK Incident Management (Fortsetzung)