Information Technology Reference
In-Depth Information
9HUZHQGHWH1RWDWLRQHQ
$NWLYLWLW
%HVFKUHLEWGLH$UEHLWVVFKULWWHHLQHV3UR]HVVHV
XQGIDVVWGLHVH]XVDPPHQ
9RUGHILQLHUWHU3UR]HVV
)DVWHLQHQDQGHUHQ3UR]HVV]XVDPPHQ
XQGNDQQGDPLWDXFKHLQ6WDUWRGHU(QGHUHLJQLVVHLQ
"
(QWVFKHLGXQJ
6\PEROIUHLQH9HU]ZHLJXQJ
%ODWWVSUXQJ
9HUZHLVWDXIHLQ(UHLJQLVDXIHLQHPDQGHUQ%ODWW
9HUELQGXQJVHOHPHQW
6\PEROIUGLH$EIROJHGHU$NWLYLWLWHQ
'RNXPHQW
6\PEROIU'DWHQLQHLQHUYRP0HQVFKHQOHVEDUHQ)RUP
.RQWUROOEHUJDEH
9HUZHLVWDXIHLQH$NWLYLWLW
6WDUWRGHU(QGHUHLJQLV
/|VWHLQHQ3UR]HVVDXVRGHUVFKOLHWLKQDE
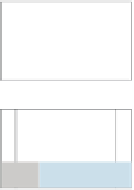
ABBILDuNG 8.10
EPK Incident Management