Database Reference
In-Depth Information
This will match any pair of nodes where the first is labeled as a
User
having the specified
name
property value, the second is labeled as a
Permission
, and there is a path of
any length between them. Finally, it returns the distinct names of all of the
Permission
nodes it has matched.
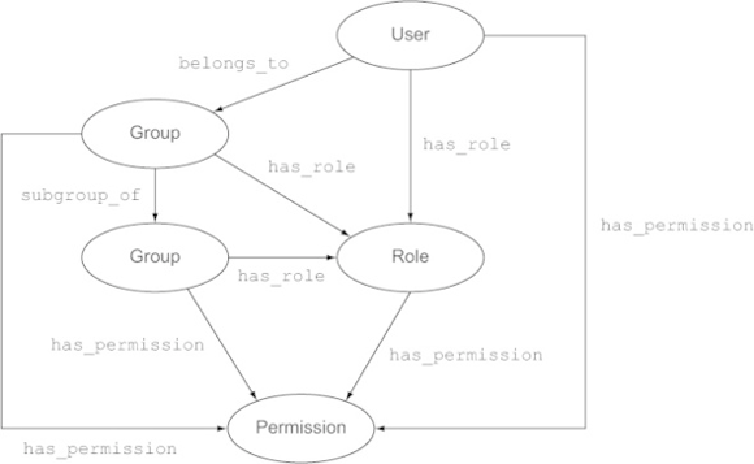
Now suppose you want to add a new feature to this model, reflecting the organization's
hierarchicalstructure.Notonlycanusersbelongtogroups,groupscanbesubgroupsoflar-
ger groups—
Testers
,
UX Designers
, and
Coders
could be subgroups of the group
group_of
relationship between groups.
Figure 2.6. The access control model extended to support subgroups
Changing the RDBMS query to support this scenario would be a non-trivial task, but the
Cypher query that worked with the initial model will work just as well with the extended
one, because it is indifferent to
how
you get from a
User
to a
Permission
.