Cryptography Reference
In-Depth Information
&
)
!
"
)
(
"-(
!
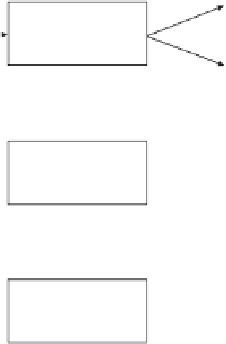
Figure 2.11
The three algorithms of a DSS with message recovery.
A DSS can be used to digitally sign messages and verify digital signatures
accordingly.
8
A
DSS with appendix
is used to generate and verify digital signatures
with appendix, whereas a
DSS with message recovery
is used to generate and
verify digital signatures giving message recovery. Note that any DSS with message
recovery can be turned into a DSS with appendix by hashing the message and then
signing the hash value.
In either case, the entity that digitally signs data units or messages is some-
times called
signer
or
signatory
, whereas the entity that verifies the digital signa-
tures is called
verifier
. In a typical setting, both the signatory and the verifier are
computing devices that are operated on behalf of human users.
The working principle of a DSS (with appendix or message recovery) is
illustrated in Figure 2.9. Having in mind the notion of a trapdoor function, it is simple
and straightforward to explain what is going on. On the left side, the signatory A uses
its private key
k
−
A
to invert the one-way function for message
m
and to compute the
digital signature
s
as follows:
s
=
D
A
(
m
)=
D
k
−
1
A
(
m
)
The signatory sends
s
to the verifier (if the digital signature is with appendix,
then
m
must also be sent along with
s
). On the right side, the verifier must use the
8
In the literature, a DSS is often called
digital signature scheme
(with the same abbreviation).