Cryptography Reference
In-Depth Information
Recall from Section 3.2.1 that if key management was easy then we would all
probably be using a one-time pad for encryption!
Note that while all cryptographic keys need to be managed, the discussion in
this chapter is primarily aimed at
keys that need to be kept secret
. In other words, we
focus on symmetric keys and the private keys of a public-key pair (that is, private
decryption or signature keys). Public keys have such special key management
issues that we devote Chapter 11 to considering them. That said, many of the
broader issues discussed in this chapter also apply to public keys.
10.1.2
The key lifecycle
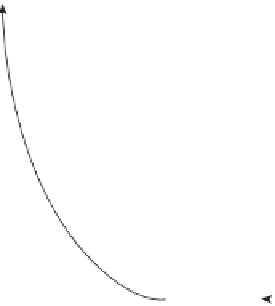
Another way of defining the scope of key management is to consider the
key lifecy-
cle
, which identifies the various processes concerning cryptographic keys through-
out their lifetime. The main phases of the key lifecycle are depicted in Figure 10.1.
Key generation
concerns the creation of keys. We discuss key generation in
Section 10.3.
Key establishment
is the process of making sure that keys reach the end points
where they will be used. This is arguably the most difficult phase of the key
lifecycle to implement. We discuss key establishment in Section 10.4.
Key storage
deals with the safekeeping of keys. It may also be important to conduct
key backup
so that keys can be recovered in the event of loss of a key and,
ultimately,
key archival
. These are all discussed in Section 10.5.
Key usage
is about how keys are used. As part of this discussion we will consider
key change
. We will also look at how a key's life ends in
key destruction
. These
are all discussed in Section 10.6.
Key
generation
Key
backup
Key
establishment
Key
archival
Key
storage
Key usage
Key
change
Key
destruction
Figure 10.1.
The key lifecycle