Cryptography Reference
In-Depth Information
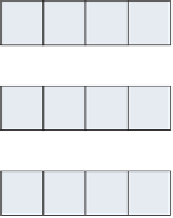
13-16; 21-24 are a permutation of key bytes 17-20; and so on. Three-fourths of the
time, this permutation is a simple XOR operation on the previous “key length”
four bytes — bytes 21-24 are the XOR of bytes 17-20 and bytes 5-8. Bytes 25-28
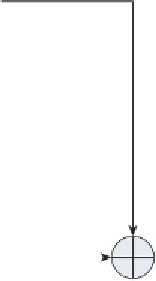
are the XOR of bytes 21-24 and bytes 9-12. Graphically, in the case of a 128-bit
key, this can be depicted as shown in Figure 2-7.
Initial Key Input
Key Schedule
bytes 1-4
bytes 5-8
bytes 9-12
bytes 13-16
bytes 17-20 =
bytes 1-4 xor
bytes 13-16
bytes 21-24 =
bytes 5-8 xor
bytes 17-20
bytes 25-28 =
bytes 9-12 xor
bytes 21-24
...
Figure 2-7:
AES 128-bit key schedule computation
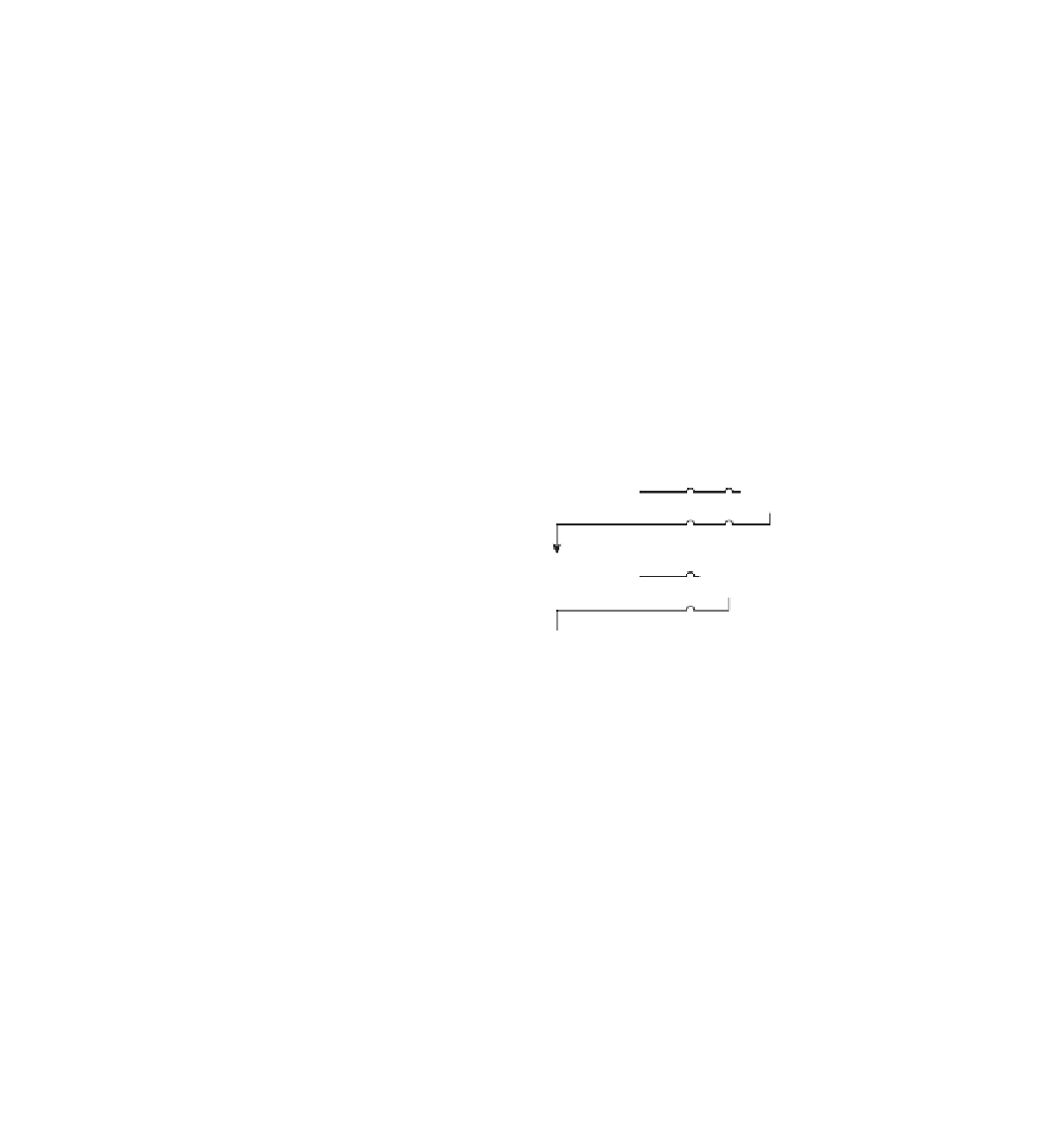
For a 192-bit key, the schedule computation is shown in Figure 2-8. It's just
like the 128-bit key, but copies all 24 input bytes before it starts combining them.
And the 256-bit key is the same, but copies all 32 input bytes.
This is repeated 44, 52 or 60 times (rounds * 4 + 1) to produce as much key-
ing material as needed — 16 bytes per round, plus one extra chunk of 16 bytes.
This isn't the whole story, though — every four iterations, there's a complex
transformation function applied to the previous four bytes before it is XORed
with the previous key-length four bytes. This function consists of fi rst rotating
the four-byte word, then applying it to a substitution table (AES's s-box), and
XORing it with a
round constant
.











Search WWH ::

Custom Search