Cryptography Reference
In-Depth Information
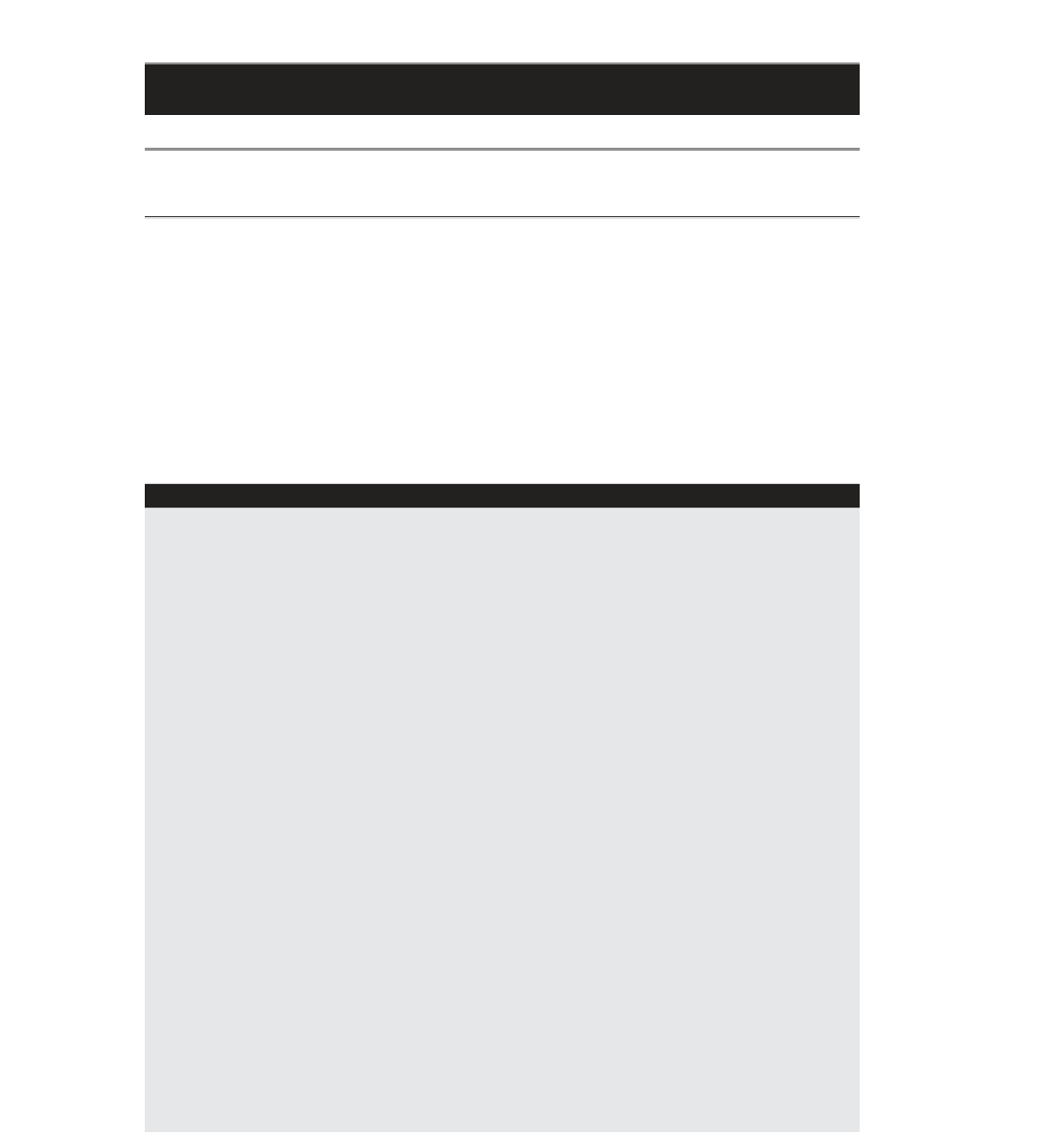
Table 5-1:
Signing Algorithm OIDs
HASH ALGORITHM
IDENTIFIER
ENCRYPTION ALGORITHM
OBJECT IDENTIFIER
MD5
RSA
2A 86 48 86 F7 0D 01 01 04
SHA-1
RSA
2A 86 48 86 F7 0D 01 01 05
SHA-1
DSS
2A 86 52 CE 38 04 03
See X.690 and RFC 2313 for more details on how these values are determined.
All you particularly care about is that the third fi eld of the certifi cate (or the sec-
ond, if the version number was not supplied) is equal to one of these three-byte
sequences. You use this value as a switch to validate the signature of the certifi cate.
NOTE
You may be wondering: “What about ECDSA?” Well, that's sort of
complicated. The topic of elliptic-curve cryptography (ECC) in X.509 is revis-
ited in Chapter 9. In general, ECC is not explicitly supported by any version of
TLS < 1.2, and supporting it in any version can get a bit hairy.
OIDs
If you read any of the ITU X series specifi cation documents, you'll notice that
the OIDs are not given in hexadecimal form as they are in Table 5-1. Instead,
they're given in a
dotted-decimal
form such as 1.2.840.113549.1.1.4. However,
in order to be used, they must be converted to the hexadecimal forms shown in
this topic. The X.690 specifi cation details this conversion authoritatively. You
don't actually need to know how to convert from these dotted-decimal num-
bers to the normalized hexadecimal forms in order to use them. I've converted
all of the ones you need to know but if you're curious, read on.
An OID in X.509 is a leaf in a very, very large tree structure. For example,
the OID for the MD5withRSA signature algorithm is 1.2.840.113549.1.1.4. Each
number in this very long digit string identifi es an element in a large hierarchy.
1 represents iso; 1.2 represents iso/memberBody; 1.2.840 represents iso/
member-body/usa and so on. All in all, the OID in this example represents
iso/memberBody/usa/rsadsi/pkcs/pkcs1/MD5. Each number only has meaning
relative to what came before it. The RSA corporation controls the 1.2.840.113549
namespace
and they use 1.1.4 to identify rsa with pkcs #1 padding md5.
So how do you get from 1.2.840.113549.1.1.4 to 2A 86 48 86 F7 0D 01 01 04?
Well, the 01 01 04 part is pretty obvious: This is the byte representation of the
digits 1.1.4. But as you can see, even the third numeral, 840, is too large to fi t
into a single byte. Rather than include separators, they adopted a variable-
length encoding scheme (The X.500 family of specifi cations, which includes
X.509, is big on variable-length encoding schemes). The 86 48 represents 840,
and the 86 F7 0D represents 113549. The encoding scheme used here is this: If
the high-order bit is 1 then the other seven bits in this byte should be concat-
enated with the
next
byte. If the high-order bit is 0 then this is the last byte in






Search WWH ::

Custom Search