Cryptography Reference
In-Depth Information
(d) Store all quartets (
l
C,
i
u
C
∗
,
v
C
,
j
w
C
∗
) defined by all pairs (
l
C,
i
u
C
∗
)
∈H
and (
v
C
,
j
w
C
∗
)
2
15
.
84
and 1
2
40
in a
∈I
, for all 1
≤
i, j
≤
≤
l, u, v, w
≤
.
(e) For all quartets (
l
C,
i
u
C
∗
,
v
C
,
j
w
C
∗
)in
hash table
J
, do filtering by the following
steps. In each steps, discard the quartets which do not satisfy the con-
ditions and if less than 3 quartets are remained, then go to Step 2 with
another key guessing.
i. Check if
l
C
[0
,
1]
J
v
C
[0
,
1] = 0,
i
u
C
∗
[0
,
1]
j
w
C
∗
[0
,
1] = 0,
l
C
[2]
⊕
⊕
⊕
j
u
C
[2]
,and
v
C
∗
[2]
j
w
C
∗
[2]
(2
−
42
filtering).
∈E
⊕
∈E
ii. Compute and check if
l
X
31
[3]
j
u
X
31
[3]
,and
v
X
31
[3]
j
w
X
31
[3]
⊕
∈F
⊕
∈
(2
−
8
filtering).
iii. Check if Pr[(
F
0
(
l
C
[6]
F
u
C
[6])
,
0)
l
C
[7]
u
C
[7]]
>
0andPr[(
F
0
⊕
→
⊕
j
w
C
∗
[6])
,
0)
(
v
C
∗
[6]
v
C
∗
[7]
j
w
C
∗
[7]]
>
0(2
−
5
.
65514
filtering).
⊕
→
⊕
iv. Compute
ΔT
=
l
X
30
[4]
u
X
30
[4] and
ΔT
=
v
X
30
[4]
j
w
X
30
[4], and
⊕
⊕
check if Pr[(
F
1
(
ΔT
)
,
0)
→
u
C
[6]]
>
0andPr[(
F
1
(
ΔT
)
,
0)
→
l
C
[6]
⊕
j
w
C
∗
[6]]
>
0(2
−
5
.
65514
filtering).
v. Compute and check if Pr[(
F
1
(
l
X
31
[4]
v
C
∗
[6]
⊕
u
X
31
[4])
,ΔT
)
⊕
→
i
l
C
[5]
⊕
j
w
X
31
[4])
,ΔT
)
→
u
C
[5]]
>
0andPr[(
F
1
(
v
X
31
[4]
v
C
∗
[5]
j
w
C
∗
[5]]
>
⊕
⊕
0(2
−
4
.
69704
filtering).
vi. If 3 or more quartets (
l
C,
i
u
C
∗
,
v
C
,
j
w
C
∗
) remained, record them and
go to Step 3; otherwise, go to Step 2 with another guess.
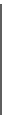
0
0
0
0
0
10
30r
ͷ
͡
ͷ
͢
ͷ
͡
ͷ
͢
2-(e)-v
2-(e)-ii
0
࣠
0
0
31r
ͷ
͡
ͷ
͢
ͷ
͡
ͷ
͢
2-(e)-iv
10
2-(e)-iii
0
0
ࣟ
: Guessed key bytes
: Check points
2-(e)-i
Fig. 3.
Filtering of wrong quartets. The numbers nearby the check points indicate the
corresponding steps from 2-(e)-i to 2-(e)-v.
Counting and sorting
3. In the following step 4 to step 12, discard the quartets with each key bytes
guessed in each step which do not satisfy conditions. In each steps, if less
than 3 quartets are remained, then go to Step 2 with another key guessing.
4. Guess the
LSB
4
(
K
1[15]) to compute
LSB
4
(
SK
1[126]) and its related keys.
For each key and remained quartet, check (a)
LSB
4
(
l
X
29
[3]
u
X
29
[3]) = 0
⊕
and (b)
LSB
4
(
v
X
29
[3]
j
w
X
29
[3]) = 0.
⊕















































































































Search WWH ::

Custom Search