Cryptography Reference
In-Depth Information
a a
b
b
Round
10
t
1
1
t +
1
11
2
1
1
t +
2
11
122
12
t +
3
11
1222
122
t +
4
11
12222 1222
t +
5
11
42222212222
t +
6
14
5555542222322222
t +
7
45
555554222332222
t +
8
55
55555422333222
t +
9
55
5555542333322
t +
10
55
555554333332
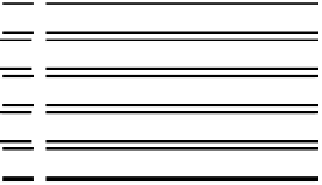
Fig. 4.
The obtained bytes of sixteen 8-byte buffers
b
at any round by executing each
attack step. Number
i
(
i
=1
, ··· ,
5) represents the bytes obtained at Step
i
.
Since the attacker knows
a
(
n
)
1
and
a
(
n
)
1
(
b
(
n
)
10
⊕
≪
17
)(
n
=
t
+1
,...,t
+5), he
can calculate
b
(
n
)
10
(
n
=
t
+1
,...,t
+ 5). By the characteristics of
ρ
-function, he
also obtains
b
(
n−
1
4
(
n
=
t
+1
,...,t
+ 5) shown in Fig.3 (b).
As a result, the attacker can obtain
b
(
n−
1)
4
and
b
(
n
)
10
(
n
=
t
+1
,...,t
+5)
with 12
.
54(= 2
.
09
6) pairs of correct and faulty outputs. Each byte of the
buffer obtained at each step is shown in Fig.4. Number
i
in Fig.4 means that
the attacker obtains its location in each round at step
i
and the locations of the
8bytesof
b
4
and
b
10
are shown as heavy lines because the attacker only knows
these bytes from the
ρ
-function.
×
Step 2: Obtain Intermediate State from the Shift Operation in the
λ
-Function.
By the structure of the
λ
-function, the attacker obtains another
parts of the buffer shown in Fig.4 using buffers obtained in Step 1.
Step 3: Obtain Intermediate State from the XORed Operation in the
λ
-Function.
The attacker also obtains another byte of the buffer through the
feed-back of the XORed operation of the
λ
-function. As an example, when the
attacker knows
b
(
t
)
4
and
b
(
t
+2)
10
,healsoknows
b
(
t
+6)
10
shown in Fig.5. Using this
characteristic, he can obtain
b
10
also used in the
ρ
-function as a parameter by
only calculating the
λ
-function.
Step 4: Obtain Intermediate State from the
ρ
-Function
Since the at-
tacker already knows
b
(
t
+6)
10
by calculating the
λ
-function in Step 3, he immedi-
ately calculates
a
(
t
+6)
1
from
a
(
t
+6)
1
(
b
(
t
+6)
10
⊕
≪
17
) obtained in Step 1. Then, he
also obtains
a
(
t
+6)
1
(=
a
(
t
+7)
0
)and
b
(
t
+5)
4
.





















































































Search WWH ::

Custom Search