Cryptography Reference
In-Depth Information
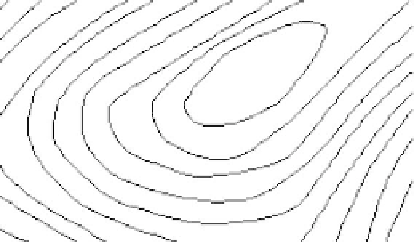
Fig. 6.9.
Watermarked map.
1.
Invisibility
The resulting map watermarked by the scheme is shown in Fig. 6.9. This
indicates the schemes better invisibility. Comparing with Fig. 6(b), the
shape-distortions induced by the algorithm are obviously lower than former
works. By choosing D
o
as the cover data, the data embedding procedure
can preserve the local shapes of the original map.
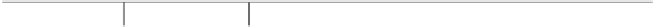
Table 6.1.
Results of robustness tests for map simplification and interpolation.
Threshold(m)
0.2
0.4
0.6
0.8
1.0
simplification
dis(f
a
,f
b
)
0.14593
0.20967
0.18385
0.21114
0.32018
Stepwidth(m)
1.0
0.8
0.6
0.4
0.2
Interpolation
dis(f
a
,f
b
)
0.087374 0.094742 0.093985 0.092177 0.092762
2.
Robustness
The selected cover data D
o
is invariant to map translation and rotation.
The division of D
o
is independent on the storage order of the map objects.
As a result, the proposed scheme is inherently robust to translation, ro-
tation and data reordering. The robustness tests then focus on the most
serious forms of attacks to vector map watermarking schemes such as map
simplification, interpolation and low-amplitude noise. For map simplifica-
tion, Douglas-Peucker algorithm is used with the threshold range [0,τ].
The Cubic Spline Algorithm is adopted for map interpolation with a se-
ries of stepwidths. All detecting results are shown in Table 6.1. Taking the
threshold T =0.068, the watermark can be successfully defended under
each attack. This demonstrates the schemes robustness to above attacks.
Additive noise attack mainly comes from some daily works (e.g. map for-
mat transformation) and generally has small amplitude. Given a map for
detecting, a series of imposed additive noises with the amplitudes from 0.01m
to 0.1m to it to simulate the noise attack procedures. For each noise ampli-
tude, the attacking and the corresponding detecting procedures are repeated