Cryptography Reference
In-Depth Information
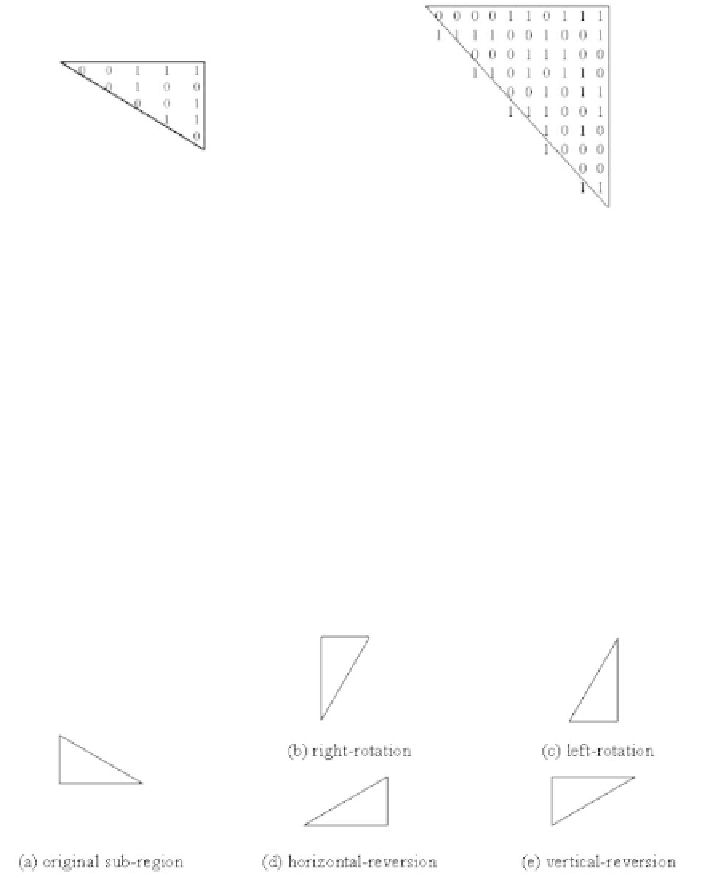
(a) the orignal binary sub-region (b) one of the shadows of the sub-region
Fig. 4.7.
An example of a binary sub-region and ont of its generated shadows.
structed shadow α
j
, and moves the i-th sub-shadow b
i
to the rb
i
-th location
of the newly constructed shadow β
j
.
However, the shape of the sub-shadow may not fit in with that of the
new location. Hence, the scheme uses right-rotation, left-rotation, horizontal-
reversion, and vertical-reversion operations to change the shape of the sub-
shadow. A sub-region example after four operations is shown in Fig. 4.8. Let
a
j
1
,a
j
2
,, and a
j
2
k
,andb
j
1
, b
j
2
,,andb
j
2
k
be the new generated sub-shadows.
Next, the scheme respectively combines the sub-shadows, a
j
1
,a
j
2
,, and a
j
2
k
,
and b
j
1
, b
j
2
,,andb
j
2
k
to form the shadows α
j
and β
j
, for the plane P
j
.
Fig. 4.8.
An example sub-region after four operations.
Finally, the scheme collects the sub-shadows generated for each plane in
order to compose the final shadows, which are expressed as
S
1
= α
1
2
7
+ α
2
2
6
++ α
7
2
1
+ α
8
,
and
(4.5)
S
2
= β
1
2
7
+ β
2
2
6
++ β
7
2
1
+ β
8
.
(4.6)