Java Reference
In-Depth Information
Approaching the Java security API
Java EE security services provide a robust and easily configurable security mechanism to
authenticate users and authorize access to application functions and the associated data. To
better understand the topics related to security, we should first lay out some basic defini-
tions:
•
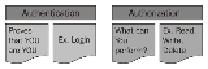
Authentication
: This is the process by which you can verify who is currently ex-
ecuting an application, regardless of whether it is an EJB or a servlet (and so on).
Authentication is usually performed by means of a
Login
module contained in a
web/standalone application. The Java EE specification provides only general re-
quirements that must be met by all compliant containers. This means that every ap-
plication server provides its own authentication mechanisms, which is a problem
when it comes to portability of applications and their configuration.
•
Authorization
: This is the process by which you can verify if a user has the right
(permission) to access system resources or invoke certain operations. Authoriza-
tion, therefore, presupposes that authentication has occurred; it would be impos-
sible to grant any access control if you don't know who the user is first. Java EE
specification provides means to authorize a user's actions. The authorization de-
clarations are usually portable between different application servers. The differen-
ce between authentication and authorization is depicted in the following diagram:
In Java EE, the containers are responsible for providing application security. A container
basically provides two types of security: declarative and programmatic. Let's take a look at
both of them:
•
Declarative security
: This expresses an application component's security require-
ments by means of deployment descriptors. Because deployment descriptor in-
formation is contained in an external file, it can be changed without the need to
modify the source code.