Cryptography Reference
In-Depth Information
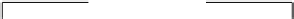
nonce
C
nonce
S
Aut.
C
→
S
Aut.
S
→
C
Enc.
C
→
S
master secret
pre master secret
PRF
PRF
Enc.
S
→
C
IV
C
→
S
IV
S
→
C
Figure 12.14.
Key derivation in SSL.
Given secret
secret
, a seed
seed
, and a string
label
we further define a sequence
PRF(
secret
,
,
label
seed
)by
,
||
⊕
,
||
PRF(
secret
,
label
,
seed
)
=
P MD5
(
S
1
label
seed
)
P SHA1
(
S
2
label
seed
)
where
S
1 and
S
2 are the two halves of
secret
. (If
secret
has an odd length, its middle
byte is both the last byte of
S
1 and the first byte of
S
2.)
PRF is used in order to compute the
master secret
. For this we just take the first
48 bytes of
=
PRF(
pre master secret
,
“
master secret
”
,
nonce
C
||
nonce
S
)
.
master secret
As illustrated in Fig. 12.14, PRF is also used in order to generate a key block from the
master secret as follows.
=
,
,
nonce
S
||
key block
PRF(
master secret
“
key expansion
”
nonce
C
)
This key block is the concatenation of the four secret keys and the two initial vectors
which are used in the cipher spec.
PRF is also used to compute the two 12-byte MAC of the handshake (one
MAC
C
from the client, one
MAC
S
from the server) by
h handshake
=
MD5(handshake)
||
SHA1(handshake)
MAC
C
=
PRF(
master secret
,
“
client finished
”
,
h handshake)
MAC
S
=
PRF(
master secret
,
“
server finished
”
,
h handshake)
where handshake is the concatenation of all handshake messages.
12.4
PGP: Pretty Good Privacy
Unlike SSL which is dedicated to security of on-line communication, PGP brings
security in an off-line way: signature and encryption of e-mails, archives, etc. PGP was






















Search WWH ::

Custom Search