Information Technology Reference
In-Depth Information
3
Our Adaptive System Model
3.1
The Robust Data Origin Authentication Model
Our protocol combined the IDA and the Merkle HASH tree to construct a kind of
trusted data origin authentication model [11] that can resist both the packet loss and
the pack injection within the threshold values.
The IDA [12] is constructed with two important parameters
n
and
m
. The file to be
encoded can be segmented into
n
pieces. And only
m
pieces of File are given, we can
reconstruct File according to the steps of IDA.
In our method, firstly two important encode parameters have to be set:
n
and
m
.
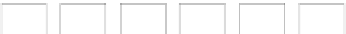
Then we use the Merkle HASH tree as the base framework, dividing a block of data
into
n
packets and then construct the Merkle HASH tree as Fig. 1.
h
−
Hh
(
||
h
)
07
03
−
47
−
h
−
h
−
Hh
(
||
h
)
Hh
(
||
h
)
03
47
45
−
67
−
01
−
23
−
h
−
h
−
h
−
h
−
Hh
(||
h
)
Hh
(||
h
)
Hh
(||
h
)
Hh
(||
h
)
01
0
1
23
45
67
2
3
4
5
6
7
h
h
h
h
h
h
h
h
HP
()
HP
()
HP
()
HP
()
HP
()
HP
()
HP
()
HP
()
P
P
P
P
P
P
P
P
Fig. 1.
The Merkle HASH tree of 8 nodes
Secondly we get the concatenation value
F
=
H
(
P
0
)||
H
(
P
1
)||…||
H
(
P
n
-1
) and the signa-
ture of the group
˃
(
K
public
,
H
(
F
)). Next using IDA, we can encode and disperse both
the concatenation value and the signature into n pieces as {
F
0
,
F
1
,…,
F
n
-1
} and {
˃
0
,
˃
1
,…,
˃
n
-1
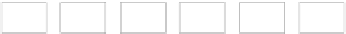
}. So a complete packet
i
includes three parts as Fig. 2, the data block
P
i
itself, the hash and signature segments
F
i
and
˃
i
, and all the related hash values of the
brother nodes from it to the root in the Merkle HASH tree, such as {
h
0
,
h
2-3
,
h
4-7
} to
packet
P
1
in Fig. 1.
P
F
,
σ
{
hh
,
,...,
h
}
i
i
ab
z
Fig. 2.
Three parts of one packet
According to the IDA, as long as
m
in the
n
pieces of
F
i
or
˃
i
received, the intact hash
value or signature can be recovered, and then the data can be authenticated. So it can
tolerate the packet error in the range of
m
. Then for the packet injection or forgery,
the Merkle HASH tree can guarantee that the forged packets are recognized based on