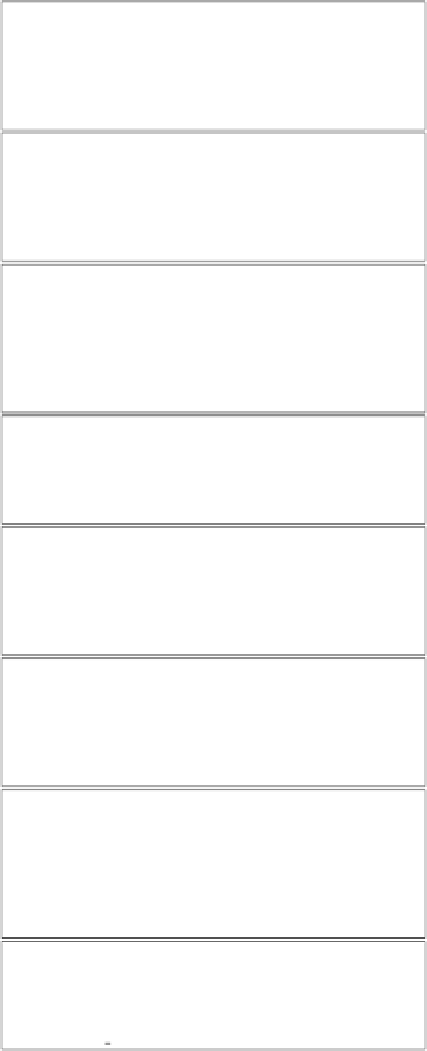
Information Technology Reference
In-Depth Information
Action
touch
(
Agent, F ile
)
Detectime:
timestamp
Pre:
OperatingSystem
(
OS
)
Post:
file
(
File
)
,
authorized
(
Agent, read, F ile
),
authorized
(
Agent, write, F ile
)
Action
block
(
Agent, Printer
)
Detectime:
timestamp
Pre:
printer
(
Printer
)
,
physical access
(
Agent, Printer
)
,
not(
blocked
(
Printer
))
Post:
blocked
(
Printer
)
Action
lpr
-
s
(
Agent, Printer, F ile
)
Detectime:
timestamp
Pre:
printer
(
Printer
)
,
file
(
File
)
,
authorized
(
Agent, read, F ile
)
,
OperatingSystem
(
OS
)
Post:
queued
(
F ile, Printer
)
Action
remove
(
Agent, F ile
)
Detectime:
timestamp
Pre:
authorized
(
Agent, write, F ile
)
,
file
(
File
)
Post: not (
file
(
File
))
Action
ln
-
s
(
Agent, Link, F ile
)
Detectime:
timestamp
Pre: not (
file
(
Link
))
OperatingSystem
(
OS
)
Post:
linked
(
Link, F ile
)
file
(
File
)
Action
unblock
(
Agent, Printer
)
Detectime:
timestamp
Pre:
printer
(
Printer
)
,
blocked
(
Printer
)
,
physical access
(
Agent, Printer
)
Post: not (
blocked
(
Printer
))
Action
print
-
process
(
Printer, Link
)
Detectime:
timestamp
Pre:
queued
(
Link, Printer
)
,
linked
(
Link, F ile
)
,
not (
blocked
(
Printer
))
Post:
printed
(
Printer, F ile
)
,
not (
queued
(
Link, Printer
))
Action
get
-
file
(
Agent, F ile, Printer
)
Detectime:
timestamp
Pre:
printed
(
Printer, F ile
)
,
physical access
(
Agent, Printer
)
Post:
read access
(
Agent, F ile
)
Fig. 1.
Definition of actions used in the illegal file access scenario