Information Technology Reference
In-Depth Information
field of each module indicates the module's invoking order of the policy module
chain. The “type” field of each module has one of following value: null module
which means the module does not make decision, grant module which means
grant the access right even it is not allowed by the modules invoked later, con-
straint module which means the denial result be returned to the enforcement
part immediately, grant-constraint module which means immediately return the
decision to the enforcement part. SECIMOS enables runtime changing a mod-
ule's type and order to resolve conflicts, and is an effective step towards the
adaptive secure operating system. This paper doesn't discuss the principles of
LSM and module coordinator further. We will introduce four policy models used
SECIMOS rest of this section. In current implementation of SECIMOS all se-
curity policy modules are constraint modules. The system will deny an access
request if any one of four modules denies the request. This greatly alleviate the
job of formalization of SECIMOS as a whole because the security assurance is
distributed in series.
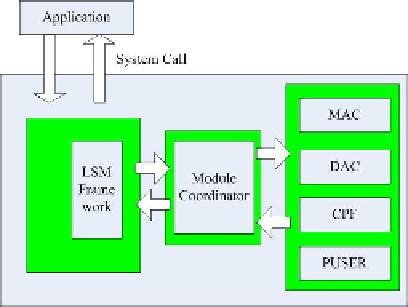
Fig. 1.
Basic Architecture of SECIMOS
2.1
Mandatory Access Control (MAC) Policy Model
Our MAC policy model takes [9] approach which is a refinement of BLP model
for networks [10]. Below, the set of security properties associated with our model
are presented. Otherwise specially point out, the notions such as subjects set S,
objects set O, set of access modes A , security level mapping function level are the
same as in [10] or [3]. In our model, level function class f consists of four level
functions: level(
O
), level(
S
), v-max(
S
) and a-min(
S
). Functions level(
O
)and
level(
S
) are the same as before. However, the current-level(
S
) function is replaced
by two new functions, v-max(S) and a-min(S). v-max(S) represents the maxi-
mum sensitivity at which a subject may view an object and a-min(S) represents
the minimus sensitivity at which a subject may alter an object. It is required that
for all subjects
S
: level(
S
)
a-min(
S
). The subset
of security levels defined by inclusive range between v-max(
S
) and a-min(
S
)is
≥
v-max(
S
) and v-max(
S
)
≥