Database Reference
In-Depth Information
•
Choose two large, random prime numbers n1 and n2.
•
Compute the product of n1 and n2. This product is also known as the limit L,
assumed to be larger than the largest integer ever needed to be encoded.
•
Choose a prime number larger than both n1 and n2 as the public key P
•
Choose the private key R in a special way based on n1, n2, and P
[If you are interested, R is calculated such that R * P = 1, modulo (n1-1) * (n2-1).]
The limit L and the public key P are made known publicly. Note that the private
key R may be computed easily if the public key P and the prime numbers n1 and
n2 are given. However, it is extremely difficult to compute the private key R if just
the public key P and the limit L are known. This is because finding the prime factors
of L is almost impossible if L is fairly large.
Data Exchange Example
Let us consider the use of public key encryption in a
banking application. Here are the assumptions:
•
Online requests for fund transfers may be made to a bank called ABCD. The
bank's customer known as Good places a request to transfer $1 million.
•
The bank must be able to understand and acknowledge the request.
•
The bank must be able to verify that the fund transfer request was in fact made
by customer Good and not anyone else.
•
Also, customer Good must not be able to allege that the request was made up
by the bank to siphon funds from Good's account.
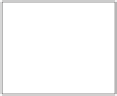
Figure 16-12 illustrates the use of public key encryption technique showing the
banking transaction. Note how each transfer is coded and decoded.
ABCD Bank
Public Algorithm:
Encryption EE,
Decryption DD
Private Key:
ABCD-d
Meaningless
Text
Fund Transfer
Request
Apply
Good-e, EE
Meaningless
Text
Apply
ABCD-d,
DD
Meaningless
Text
Fund Transfer
Request
Private Key:
Good-d
Apply
ABCD-e,
EE
Public Keys
ABCD-e
Good-e
Apply
Good-d, DD
Customer Mr. Good
Figure 16-12
Public key encryption: data exchange.



























Search WWH ::

Custom Search