Information Technology Reference
In-Depth Information
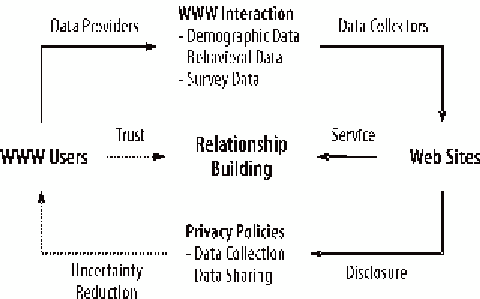
Figure 1. Data privacy and uncertainty reduction
comply with what they stipulate in their policies,
their data handling behavior is predictable, which
may help them to build trusting relationships
with users. Once a relationship of trust has been
established between users and companies, users
may be more willing to divulge personal infor-
mation, which may lead to even more enhanced
customer service, more customized Web sites,
and eventually customer loyalty.
sample size compares favorably with other con-
tent analysis studies (Daly et al., 2004; Döring,
2002; Kolbe & Burnett, 1991; O'Connor, 2003;
Ryker et al., 2002). All Web sites included in the
sample collect personally identifiable information
when users register with the site or place orders.
While being essentially a convenience sample, the
selected privacy policies stem from companies
covering a broad spectrum of business models
and industries. They include companies selling
goods and providers of services; pure e-brands
and off-line brands with online outlets; and B2C
online stores and C2C auctions. Also, they belong
to four different industries, including retail, travel,
Internet services, and news. This sampling method
was adopted to ensure the inclusion of a diverse
range of businesses to which WWW interactions
are vital. However, the sample was not intended
to be representative of commercial Web sites, as
the purpose of this study was to identify starting
points for improving existing privacy policies.
The sample companies were chosen on the
basis of their commercial success, as successful
Web sites were assumed to serve as lead innova-
tors for other Web sites. The companies in the
Retail category were taken from the top-per-
forming companies of
Store
magazine's ranking
of the most successful Internet retailers (Reda,
2000), ignoring Web sites of conglomerates,
methodology
To examine systematically (1) what data handling
practices companies engage in, (2) which ones
they do not engage in, and (3) whether they fail
to address important areas of concern to users, a
content analysis of privacy policies was conducted
to scrutinize their content in a systematic manner,
taking into account both what is in a text and what
is not. Further, a computer-assisted textual analysis
was performed to uncover lexical patterns that
raise rather than reduce the level of uncertainty
in privacy policies.
sampling
The privacy policies of 50 well-known Web sites
were used for the analysis (see Appendix A). This
Search WWH ::

Custom Search