Hardware Reference
In-Depth Information
6.
Now we can mount the vault using the following command:
pi@raspberrypi ~ $ sudo mount -o uid=1000,gid=1000 /dev/mapper/
myvault ~/vault
The user ID/group ID arguments that we specify here are specifically for the
FAT32 filesystem. It ensures that the
pi
user (which has an uid/gid of
1000
)
will be able to write to the
~/vault
directory. With an
ext4
filesystem, these
extra flags are not necessary because the permissions of the directory itself
determine access.
That's all there is to it. You can now start filling up the
~/vault
directory. Use
df -h
~/vault
to keep an eye on the space available in the vault.
To safely close the vault, you need to unmount it first with the following command:
pi@raspberrypi ~ $ sudo umount ~/vault
Now most importantly, remember to lock your vault:
pi@raspberrypi ~ $ sudo cryptsetup luksClose myvault
To make the daily locking/unlocking routine a little less tedious, you can define
these aliases:
alias vaulton='sudo cryptsetup luksOpen ~/myvault.vol myvault && sudo
mount -o uid=1000,gid=1000 /dev/mapper/myvault ~/vault'
alias vaultoff='sudo umount ~/vault && sudo cryptsetup luksClose
myvault'
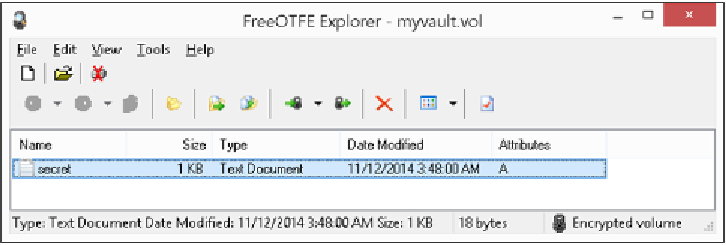
To access your vault from Windows, try FreeOTFE Explorer. It's a portable
application and very easy to use. Download it here:
http://www.intestinate.com/
Install the application, copy your vault file from the Pi with
pscp
or Dropbox,
and unlock it in FreeOTFE Explorer using your passphrase.
Accessing an encrypted file container with FreeOTFE Explorer