Database Reference
In-Depth Information
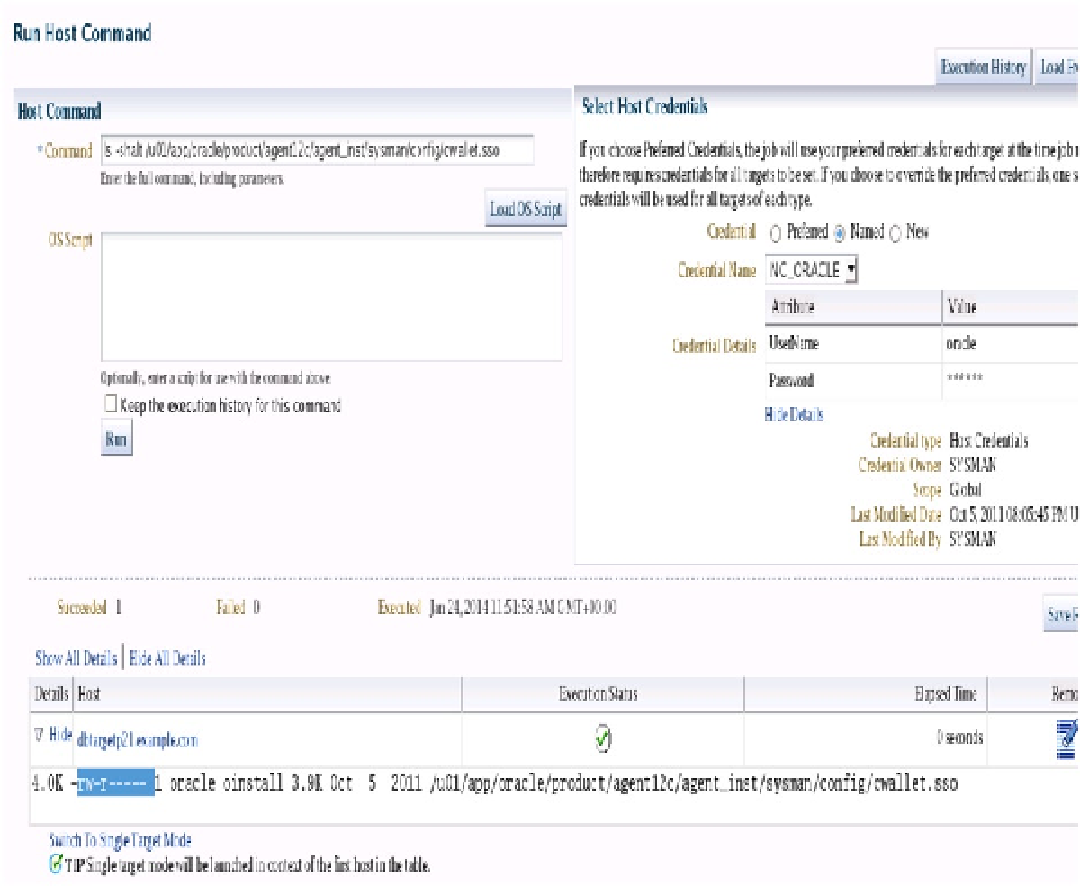
You can run your OS host command directly or run it as a script. This example has enabled us to list all the
wallets on that OS, but can we modify those wallets so we can see the command that SYSMAN ran on the target host?
The command has checked to see the perms on the wallet. The return value was such that they can write and delete
the wallet if they so wished (Figure
17-13
).
Figure 17-13.
EM12c host command to list privileges on the wallet
Now the EM user can see the perms on the wallet. We need to make sure they don't accidentally overwrite it or
make an unauthorized copy. It is certainly recommended that a lower-read privilege is used for day-to-day “BAU”
work (BAU = Business as Usual)
How else could a malfeasant user attempt to abuse EM OS access?