Image Processing Reference
In-Depth Information
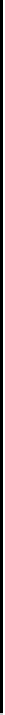
Algorithm 7: DETECT-ADSS to find out the ordered list A of end
points of ADSS in the input curve S that contains the chain code for
each connected component.
Procedure ADSS-PARAMS (S, u)
1. i ← u, l ← 1
2. if S[i] = S[i + 1] then
3.
Algorithm DETECT-ADSS (S)
1. A←{1}, u ← 1
2. ADSS-PARAMS (S, u)
3. c ← l
4. if
s
−
n
(mod 8) = 1
← S[i]
4. find
s
(=
n
) after S[i + 1]
5. l ← leftmost run length of
n
then go to Step 20
5. p ← q ← next run-length of
n
6. else
7.
(
n
,
s
) ← (S[i], S[i + 1])
6. d ← e ← round(p/2)
7. c ← c + 1 + p
8. if l −p > e
then go to Step 20
9. while q −p > d
10.
8. i ← i + 1
9. while S[i + 1] ∈{
n
,
s
}
10. if S[i] = S[i + 1] then
11. if S[i] =
s
then
12. swap
n
and
s
k ← next run-length of
n
13. l ← 0
14. return
15. else
16. i ← i + 1
17. return
11. if l −k > e then
12. c ← c + 1 + k
13. break
14. if k −p 6 e
then c ← c + 1 + k
15. else c ← c + 1 + p + e
16. if k < p then
17. p ← k
18. d ← e ← round(p/2)
19. if k > q then q ← k
20. u ← u + c
21. A←A∪{u}
22. u ← u + 1
23. repeat from Step 2
until S is finished
While checking R1 in Step 4 or Step 10, if an expected
n
or
s
is not
found at the desired place in S
k
, then the current ADSS, L
(k
i
ends with the
previously checked valid characters. This is explicit in Step 4 and implicit in
Step 10. Thus L
(k
i
satisfies R1, and is maximal from its starting point and the
finishing end, since either it is the first ADSS in S
k
, or the previous ADSS,
L
(k)
i−1
, was maximal.
Now, for each new run (of
n
), (c1) is verified in Step 9—excepting the
leftmost run, l, which is not required since p (and q) does not exist for a single
run—after appropriately updating p and q in Step 17 and Step 19, respectively,
whenever necessary. In Step 9, if it is found that q is unacceptably large (i.e.,